How Are Jailbreaks Found and How Do They Work? iOS Kernel Exploitation Presentation Gives the Technical Details
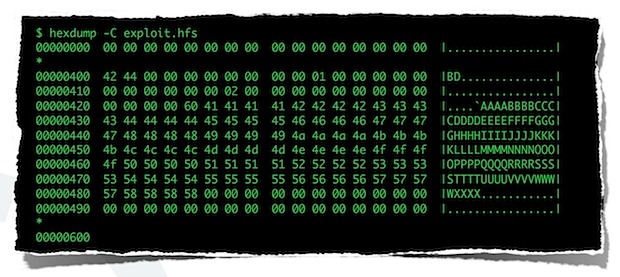
Renowned jailbreaker i0n1c, aka Stefan Esser, has put together a rather extensive presentation titled “iOS Kernel Exploitation” that explains exactly how jailbreaks work, ranging from how the exploits are found, how new code is injected into the iOS devices, how untethers work, and so much more. It was presented live at last months Black Hat security conference, but now the slides are freely available on the web for all to see.
The 97 slide presentation includes the following main topics and dives into very specific details:
- Introduction
- Kernel Debugging
- Kernel Exploitation
- Stack Buffer Overflows
- Heap Buffer Overflows
- Kernel patches from Jailbreaks
This is a fairly technical read with plenty of code samples, making it an extremely interesting look into the world of jailbreaking and iOS security. It’s pretty much a must read for anyone interested in security, development, iOS, Mac OS X, or just jailbreaking in general.
Download the presentation slides in PDF format here (.pdf) or check out the embed below:
These jailbreakers are a pretty smart group of people, it’s no wonder Apple and Facebook are busy hiring them!
Heads up to @pod2g and @i0n1c on Twitter, you can follow @osxdaily on there too.


This genius should exploit and unlock the bootloader on the Galaxy s7 so that we can get aosp
[…] via OSXDaily […]
[…] via OSXDaily […]
[…] via OSXDaily […]
[…] [osdaily] […]
Apple already knows that. :/
Apple is going to love this, LOL
Great stuff. I don’t really understand it but I’ve always admired all kinds of hackers!!!