Install Java in OS X Mountain Lion
If you need to use Java, installing the Java Runtime Environment (JRE) in OS X Mountain Lion is necessary even if you had Java previously installed in OS X Lion or Snow Leopard and just performed an upgrade to 10.8. That’s because Mountain Lion uninstalls Java during the upgrade process, this is to insure the newest version of the runtime is installed on the Mac for those who need it and leaving it out for those who don’t, theoretically preventing some potential security problems with Java like the old Flashback trojan.
Installing Java in OS X Mountain Lion is easy enough and can be done two ways:
- When a Java app is opened in Safari or elsewhere you will be prompted to install Java for OS X (2012-004 currently)
- Manual command line method to force the installation
The command line installation is fast and likely preferable for many advanced users since it can be initiated at any time, here’s what to do:
- Launch Terminal from /Applications/Utilities/ and type the following command:
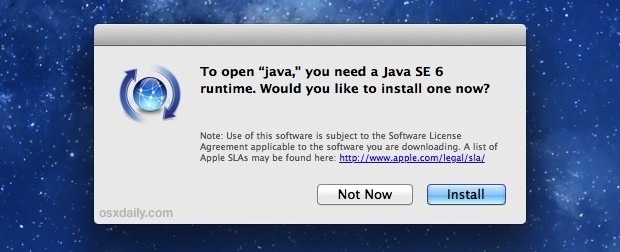
- Hit return to see a message stating “No Java runtime present, requesting install” followed by a window prompting you to install Java SE in order to open “java”, click “Install” to get the latest version
java -version
Many Mac users won’t ever need to use Java and for the average person it may be best left uninstalled. Disabling java or leaving it uninstalled remains a decent security tip to protect a Mac against some of the rare trojans and viruses floating around out there.
Thanks to Josh Penn for the great tip!


That was so painless! Many thanks!
how do you get java SE 7 on mountain lion?? there are no answers to this anywhere on the internet!
Open Java Preference App, you may find several JDKs, you can drag JDK7 to the top of the list, then re-open the shell, and invoke java -version. It will change to the JDK7.
sence there are a couple of minecraft players here this is my probelm, trying to run tekkit and every time i go to open the game this happens what can i do to fix it. also in my java options it gives me the choice of java 7 and two java 6 one 32 bit and one 64 bit
— BEGIN ERROR REPORT 5c907607 ——–
Generated 10/1/12 6:31 PM
Minecraft: Minecraft 1.2.5
OS: Mac OS X (x86_64) version 10.8.2
Java: 1.6.0_35, Apple Inc.
VM: Java HotSpot(TM) 64-Bit Server VM (mixed mode), Apple Inc.
LWJGL: 2.4.2
OpenGL: NVIDIA GeForce 9400M OpenGL Engine version 2.1 NVIDIA-8.0.61, NVIDIA Corporation
java.lang.IllegalArgumentException: Slot 194 is already occupied by immibis.tubestuff.BlockTubestuff@5081876b when adding immibis.tubestuff.BlockTubestuff@67e1ab17
at pb.(Block.java:251)
at agy.(BlockContainer.java:7)
at immibis.core.BlockCombined.(BlockCombined.java:35)
at immibis.tubestuff.BlockTubestuff.(BlockTubestuff.java:17)
at mod_TubeStuff$1.registerBlock(mod_TubeStuff.java:65)
at immibis.core.CoreProxy.RegisterBlockID(CoreProxy.java:31)
at mod_TubeStuff.load(mod_TubeStuff.java:62)
at cpw.mods.fml.common.modloader.ModLoaderModContainer.init(ModLoaderModContainer.java:356)
at cpw.mods.fml.common.Loader.modInit(Loader.java:273)
at cpw.mods.fml.common.Loader.initializeMods(Loader.java:628)
at cpw.mods.fml.client.FMLClientHandler.onLoadComplete(FMLClientHandler.java:223)
at net.minecraft.client.Minecraft.a(Minecraft.java:429)
at net.minecraft.client.Minecraft.run(Minecraft.java:738)
at java.lang.Thread.run(Thread.java:680)
— END ERROR REPORT 8d87b24f ———-
If your attempts fail to install Java updates with Mountain Lion, try quitting all browsers and internet-connected applications and install again. (This is noted in Apple’s support, but not in any windows from automated software updates.)
Doing this worked for me after several failed attempts. Slightly off topic, but found this thread when searching for answers to reinstalling with ML for use with Adobe software.
How many people in this world does not visit or use an internet bank or retirement fund site from time to time?
Well, they all need Java if Apple likes it or not. So be careful saying “I don’t need that”.
I need it a lot and is left out in the cold once again by Apple. Like Mel I can’t download the necessary Java Software. Why does Apple again think (very differently) they shall decide which software I need to use; why do they again believe they know better about MY security and MY private affairs?
I know you posted your reply more than two months ago and you’ll probably never read my reply, but I just have to reply.
I’m wondering what bank you’re using. How can a bank ever use Java (or Flash or any other plug-in)? A bank should be all about security, so they should use any plug-ins. If my bank (or any other company) would force me to use any plug-ins I’d immediately switch to another bank (or insurance company or whatever company).
I’ve never used Java and I’m really happy Apple finally decided to not install Flash and Java by default. I don’t need them and I don’t want them on my systems. I’ve never used Java, but having it installed is a big security risk, so I’m glad it’s finally gone. I’ve used Flash before, but since Apple released Lion without Flash pre-installed I’ve never installed it myself. More and more websites use HTML5 and I can easily live without those websites that require Flash.
Using plug-ins in a browsers was the most stupid idea ever. Not only is it a bad idea because of the security risks, but also because of compatibility. A website should work on every device, no matter what operating system or browser is being used. Java, Flash and Silverlight are the most used plugins. None of them are available for iOS (luckily!), I think Android only has Flash, Linux has a crappy implementation of Silverlight (Moonlight) which is absolutely useless.
In my opinion you’re a incompetent and useless web developer if you use any plug-ins. It’s absolutely ridiculous to use Java, Flash, Silverlight or any other plug-ins. How about people running iOS, Android, Linux, BSD, a Chromebook or whatever. Even if I made my own operating system and browser I should still be able to use every website.
I agree on HTML5, no plugins, but wait:
1) for now, flash is about 40% more compatible then html5.
1) it’s very expensive to develop rich web apps in js because of all the time wasted on fallbacks, that will within a couple of years, hopefully, be useless bloatware inside your code. I’m talking 80 – 90% of your time. Fallbacks often require Flash btw.
2) I wonder why you think javascript is safer or even better then java, as3 or any other language. (for now it’s very very very slow on iphone and ipad and has infantile syntax, no datatyping, not convenient to write OOP)
3) The still sucks, and totally suck, all html5 games suck very much on ios and take you back to the nineties. The persons making html5 slightly useable all derive from the Flash community, like mr. doob (three.js) and grant skinner (create.js). Kudos!
The real reason Flash was banned on ios is that the appstore would be redundant otherwise. Apple knows it will take HTML5 years to catch up with Flash because they themselves, amongst others though, are in charge of the W3C. That’s why you have to learn ios, which is a very hard to master and rapidly changing language.
I recently updated to ML and tried to download Java using both methods you describe. Either way I receive a message saying “This update can’t be installed. The update could not be expanded, and may have been corrupted during downloading. The update will be downloaded and checked again the next time that Software Update runs.” When I check for software updates, there are none. Any thoughts?
man, thanks a lot, I really needed that!
TO BE SAFE :
1) DON’T USE ADOBE FLASH
2) DON’T USE ADOBE ACROBAT READER
3) DON’T USE JAVA
4) DON’T USE MICROSOFT OFFICE
5) DON’T USE INTERNET CONNECTION
6) DON’T USE…what else ?
YOU CAN SHUT DOWN YOUR MAC ALSO, FOR ETERNITY…
Thanks for that… and your qualifications are?
Does anyone know the offline link to downloading Java SE 6 Runtime for ML? It’s nice to have it offline for reinstallation purposes.
Here’s what I get in response to “java -version”. Does this mean I do have java?
java version “1.6.0_33”
Java(TM) SE Runtime Environment (build 1.6.0_33-b03-424-11M3720)
Java HotSpot(TM) 64-Bit Server VM (build 20.8-b03-424, mixed mode)
Either way DTS is still requesting that I install Java.
Instructions to update DTS dbsign universal web signer is here: http://militarycac.com/lion.htm#DTS_uses_Java .
Any word on how to install a JDK on mountain lion?
http://arstechnica.com/apple/2012/04/oracle-updates-java-to-se-7-for-os-x-brings-full-jdk-support/
Of course, anyone who plays Minecraft (yes, guilty as charged) will also need Java.
If you also play the game, please note you HAVE to use Java 1.6 SE as supplied by Apple. Downloading 1.7 SE direct from Oracle results in a game crash. Apparently nobody knows why just yet – 1.7 happily ran MC under Lion.
On the topic of Minecraft, my boys play it and I’ve had no end to stability issues on our Pc as a result. I’m fairly convinced it is the fault of minecraft, unsigned jar files, etc.
Now that we have a Mac, I don’t want to install it at all for fear of messing something up, though I hear its okay. Do you have any thoughts or recommendations for good resources on this topic?
Works on Lion, too.
If you have the oracle java jdk installed, mt lion it will still be available after an update from lion.
Dresden:~ jsfranko$ java -version
java version “1.7.0_04”
Java(TM) SE Runtime Environment (build 1.7.0_04-b21)
Java HotSpot(TM) 64-Bit Server VM (build 23.0-b21, mixed mode)
You don’t even have to expend the time typing the -version after, a simple ‘java’ will do it.
Also, X11 isn’t installed by default. Double clicking on the X11 app will point you at an Apple knowledgebase article which will in turn point you to the XQuartz website to download X11 for the Mac.
I installed Java but I don’t actually need it, how do I delete it or disable it?
well you can’t…
i’m quite excited that upgrading to ML removes my java that I installed in lion.
So, wait for OS X 10.9 for your case.
Yes, you can. One way (not recommended) is in terminal:
sudo rm /usr/bin/java
sudo rm /System/Library/Frameworks/JavaVM.framework
The better option is to go to ‘Java Preferences’ app in the Utilities sub-folder in Applications, and uncheck the ‘On’ box of any java versions found.
Sorry, that second command should have had the R flag, for recursive.
sudo rm -R /System/Library/Frameworks/JavaVM.framework
I had no idea that it did this thanks for the post!
Thanks. I actually triggered the installation by clicking the
Java Preferences in the Other Launchpad folder.
Network folks need to use Java cuz some web-based GUIs actually runs Java applet.
Thanks for the tip, that worked perfectly. Kind of a funny bug for Apple to have.