NTP Critical Security Update for OS X Released by Apple, All Mac Users Should Install Now
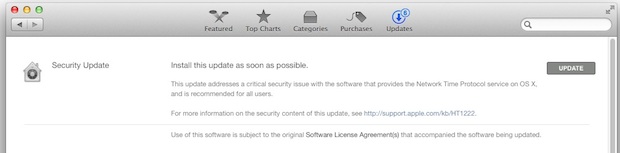
 Apple has issued a critical security update to OS X users aimed at patching an exploit with the network time protocol on most Macs. The update is labeled urgently as “Install this update as soon as possible” rather than a traditional name, perhaps indicating the importance of patching the unspecified issue with the Macs NTP.
Apple has issued a critical security update to OS X users aimed at patching an exploit with the network time protocol on most Macs. The update is labeled urgently as “Install this update as soon as possible” rather than a traditional name, perhaps indicating the importance of patching the unspecified issue with the Macs NTP.
All Mac users should heed the advice from Apple and take a moment to install the security patch.
Mac users running OS X Yosemite (10.10), OS X Mavericks (10.9), and OS X Mountain Lion (10.8) will find the update available now in the Software Update mechanism of OS X, accessible from the Apple menu and by choosing “Software Update”, the update is only 1.4MB and installs very quickly. Note that if you have automatic updates enabled for system software and security updates, the NTP was possibly installed already for you, but it’s worth checking manually anyway.
The release notes for the security update say: “This update addresses a critical security issue with the software that provides the Network Time Protocol service on OS X, and is recommended for all users”
Apple has reportedly started to automatically push the update to Mac users, according to Reuters. Those who are not sure if they have installed the update can manually check what version of NTP is installed on their Mac by issuing the following command at the Terminal:
what /usr/sbin/ntpd
Apple discusses the NTP fix here, noting the updated versions will be the following as reported by the ‘what’ command:
Mountain Lion: ntp-77.1.1
Mavericks: ntp-88.1.1
Yosemite: ntp-92.5.1
Assuming the version reported back is the same as those, the NTP patch has been installed. Some users may have seen the following notification on their Mac desktop, which indicates the patch installed itself:

Though the specific issue with Network Time Protocol (NTP) is not mentioned in the update release notes, the security update for OS X likely pertains to this remote code execution flaw in NTP that was recently discovered by Google employees.
Users should not need to reboot their Macs for any changes to take effect.
This is not necessary, but a geeky extra for those who are curious, users can manually restart the NTP server by unchecking and rechecking the “Set date and time automatically” button within the Date & Time preference panel of OS X, using ntpdate at the command line, or by killing the “com.apple.preference.datetime.remoteservice” process and reloading the Date & Time system preference panel.


I used this terminal comand- what /usr/sbin/ntpd
to see if infact the update was done via the Mac app store and to my surprise it wasn’t therefore I installed it manually and the command- what /usr/sbin/ntpd worked and showed the following- ntp 92.5.1. Why Apple update failed is beond me! Better safe than sorry! Thanks OSX Daily for the heads up!
What about Snow Leopard? Vulnerable?
After I installed this update, a map popped up on my phone. I followed the X marks the spot in my front yard. I dug down 2 feet where it told me to and found a 5 pound gold nugget!
这个更新有什么新的意义吗?在MCA没有提示,很郁闷。
Hi,
When I installed this update it also fixed the well known wi-fi issue (the one that 10.10.1 was supposed to fix)
Has this worked for anyone else?
I can now connect to my wireless router.
Interestingly, Apple’s patch didn’t change the version of ntpd: it still shows as v4.2.6 ($ ntpd –version), even after restarting the process or the entire machine.
But Apple’s method of verifying the update (from their Security Update page at http://support.apple.com/en-us/HT6601) does verify that the update took place ($ what /usr/sbin/ntpd). Not sure why they didn’t update the version number….that’s going to be confusing.
I found it right away. Thanks for the heads-up!
Yep, same for me, although I did spot a little notification saying it had been installed automatically. Normally I would go into software updates and start the install manually.
very strange. just after I posted, I saw a message flash by saying a security update had been installed. However when I went to updates, it does not show in the list of recently installed updates.
Does Apple auto install updates that are not listed?
I got the same message about 10 minutes ago. No record of what was installed other than the notification dialog.
Must be a pretty serious vulnerability.
App Store doesn’t list this update on my machine, either. I saw the message flash by this morning, butt here was no way to figure out if it was actually installed or even if it was legit.
Terrible security here. If Apple wants people’s systems to be secure, they need to do a much better job of explaining what the patch is and who initiated it and if it actually installed properly. Instead, this ham-fisted method is just going to confuse my clients and reinforce the idea that ordinary people have no hope of understanding computer security.
same here: this update is not show using either method.
Same here, went to software update and no updates shown.
I just went to the App Store and this update is not shown. Comments?
Go to About This Mac and there’s a field for Software Update.
What version of OS X are you running? Apple Menu > Software Update should have one.
If you’re on a much older version of OS X Apple may not have updated NTP on them. For those on the newest versions of OS X, if you have auto-updates installed it probably did it in the background and went unnoticed, the update is very small (1.4MB).
https://osxdaily.com/2014/11/01/automatic-install-os-x-updates-mac/