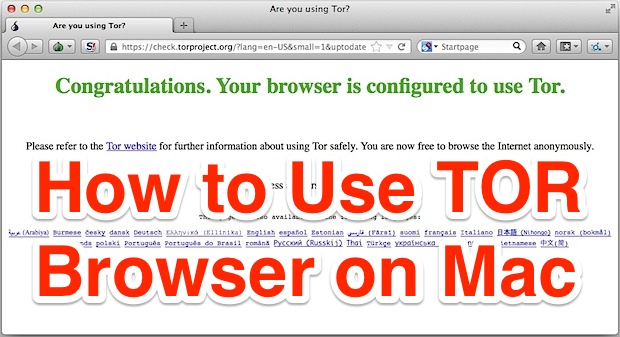
How to Use Tor on Mac to Browse the Web Anonymously & Access Blocked Websites
Tor is a free anonymity network that aims to conceal a users location and browser usage from snoopers, in addition to allowing access to websites that are otherwise blocked or filtered out through firewalls. The official description of the Tor browser and network is described as follows:
The Tor software protects you by bouncing your communications around a distributed network of relays run by volunteers all around the world: it prevents somebody watching your Internet connection from learning what sites you visit, it prevents the sites you visit from learning your physical location, and it lets you access sites which are blocked.
Though that may sound complicated, using Tor is actually quite simple. We’re going to focus on using Tor in Mac OS X, but there are Tor clients available for every significant OS, including Windows, Android, and Linux (there is currently no official iOS client).
 Before beginning you might be wondering what the point of using TOR is. For the vast majority of people, there probably isn’t a point, but Tor is very popular in certain regions of the world where internet access is restricted, monitored, or heavily filtered. For example, I have a friend who lives across the ocean in a large country with famously restrictive internet access, and many there have to use TOR or general proxy services to access fairly boring web sites the rest of us can get to without incident, like Facebook, Twitter, and Gmail. Similarly, I know many people who use Tor to be able to access those same websites through heavily restricted corporate network firewalls. Thus, many of us won’t have a need for TOR, but if you do want to be anonymous on the web, or you plan on visiting a network or country where you anticipate restrictive internet filtering and access, it can be the easiest solution to reach the outside world using communication platforms you’re already familiar with.
Before beginning you might be wondering what the point of using TOR is. For the vast majority of people, there probably isn’t a point, but Tor is very popular in certain regions of the world where internet access is restricted, monitored, or heavily filtered. For example, I have a friend who lives across the ocean in a large country with famously restrictive internet access, and many there have to use TOR or general proxy services to access fairly boring web sites the rest of us can get to without incident, like Facebook, Twitter, and Gmail. Similarly, I know many people who use Tor to be able to access those same websites through heavily restricted corporate network firewalls. Thus, many of us won’t have a need for TOR, but if you do want to be anonymous on the web, or you plan on visiting a network or country where you anticipate restrictive internet filtering and access, it can be the easiest solution to reach the outside world using communication platforms you’re already familiar with.
How to Use Tor on Mac OS X for Anonymous Web Browsing
The first thing you’ll need to do is download the free TOR client from the Tor Project, it’s available for every major operating system:
- Download Tor free from the developers
- Copy TOR into your Applications folder* and launch the TorBrowser app (OS X users may need to right-click and choose “Open” to bypass Gatekeeper)
*Technically you can run Tor off directly from a mounted image or even a USB drive, it’s up to you. If you’re going to use it often on a Mac, putting it in the Applications folder is a good idea.
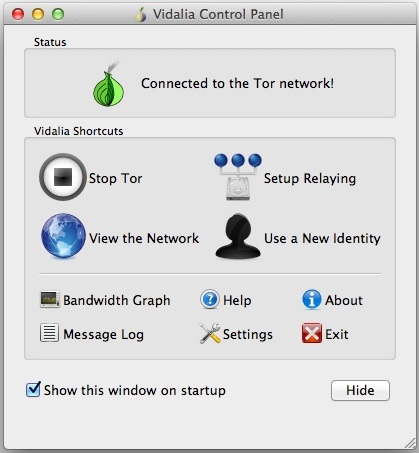
TorBrowser launches alongside an app called Vidalia, Vidalia shows you the status of the Tor network connection, let’s you adjust relaying features, checking bandwidth usage (very helpful for wi-fi hotspot use and watching data restrictions), refresh the client identity to a new IP, and quite a bit more.
The TorBrowser itself is actually just a modified version of the familiar Firefox web browser. This is what you will want to use exclusively in order to access blocked/filtered websites and to browse anonymously.
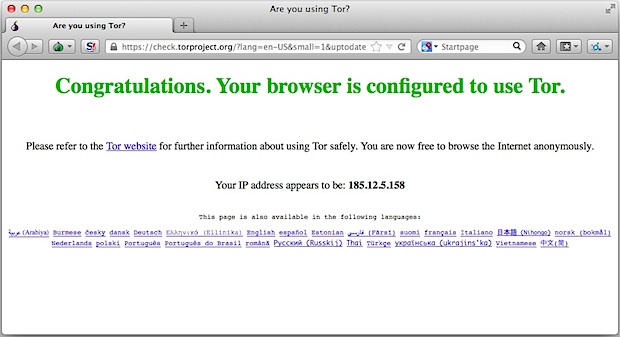
Now you can browse and use the web as usual through TorBrowser, or head on over to a .onion URL if you have one. So long as you stay in TorBrowser, you’ll be anonymous and, in some situations where access may be restricted, you should be able to access blocked websites.
Important Tor Usage Considerations
Tor is not perfect, and there are a few important things to remember when using it:
- ONLY the traffic and interaction through TorBrowser is anonymized, this means that all other apps and internet traffic continues to go through your standard external IP address as usual
- Do NOT open any documents downloaded from TorBrowser while you are online, this is because some documents and apps attempt to access the internet, which may reveal your actual IP
- Do not use or attempt to install third party browser plugins in TorBrowser, they may interfere with the anonymizing and relay features
- Browsing the web through TOR is slower than your normal internet connection due to the connection relays, so you probably won’t want to download anything substantial through TorBrowser
Not only does Tor report false IP information through the browser, but it also uses randomized fake user agent strings. In this screenshot example, the user agent of a Mac running OS X 10.9 is reported as being a Windows PC.
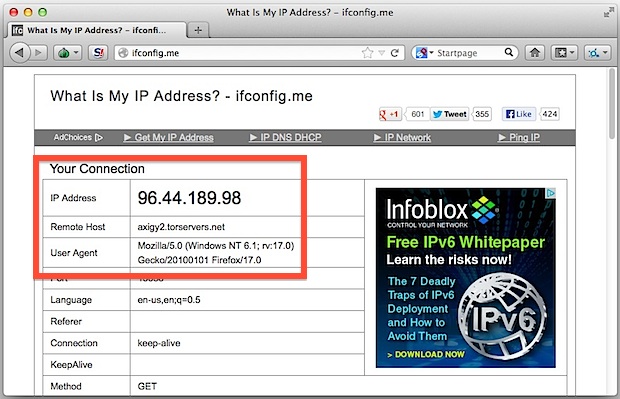
Remember, despite what is shown through the Tor client, if you query for your IP address outside of the TorBrowser you will be visible to the outside world as your normal IP. That is why it’s so important to use TorBrowser exclusively in situations where you need to access websites or remain anonymous.
By the way, if you’re currently in a nation with unrestricted and free internet access but plan on visiting a region with restricted access, you can easily test the ability of accessing blocked sites by blocking a site in your hosts file to render them inaccessible from your computer, and then use the TorBrowser client to gain access to that site despite the hosts block. Neat, huh?


Be careful using a VPN. Both Netflix and Prime restrict me from full access when I’m in France and use a VPN. Regional restrictions apply despite the fact that I’m an American subscriber and should be able to get what I pay for from anywhere including France or the Moon (my opinion). Don’t know if Tor will work or not. Will try it this summer when I go.
I have been hearing/seeing news items that say COMCAST will soon be selling to people that are interested the web sites you visit. While I don’t care who knows what I do on the web, I specifically do not want COMCAST selling this information. I am getting mixed messages as to which is better for me, TOR or VPN. Any suggestions, BTW I am not a super techy type so I need the simplest and most dependable way to do this.
Using a proxy is too many steps doesn’t provide protection. VPN is better. They each have their own merits.
I was actually wondering how to maybe block the initial communication that tor makes to acces the proxy server locally. The initial url.
I was wondering maybe I could add that to /etc/hosts to prevent others from bypassing the firewall.
Is this possible? And what would that url be?