Resolving the Mystery of a Disappearing Mouse Cursor in Mac OS X
 In an unusual and fairly rare situation, the Mac cursor can randomly disappear from OS X. More accurately, the cursor itself becomes invisible, because you can still click around on the screen but without being able to see what the mouse or trackpad is focused on.
In an unusual and fairly rare situation, the Mac cursor can randomly disappear from OS X. More accurately, the cursor itself becomes invisible, because you can still click around on the screen but without being able to see what the mouse or trackpad is focused on.
This seems to happen out of the blue, and although it is difficult to reproduce reliably, it does seem to happen more often when a Mac is running low on available memory and is using multiple monitors. Thus, you may be more likely to lose the cursor when using apps like Photoshop, or Chrome and Safari with tons of browser tabs open, especially with an external display connected. After running into this bug repeatedly I discovered a few ways to resolve the problem and make the cursor visible again.
If your mouse cursor has mysteriously disappeared in OS X, try the following tricks in descending order to bring it back:
- Hit Command+Tab to switch back to the Finder or to another app, then switch back to the active app
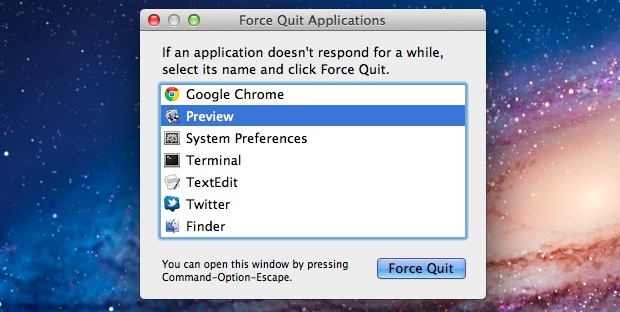
- Summon the Force Quit menu by hitting Command+Option+Escape, there is often no need to actually force quit anything as just summoning the menu is often enough to make the cursor return
- Quit and relaunch the app, or quit all apps if the cursor is gone everywhere
- Adjust the size of the cursor, found in System Preferences > Accessibility > Display to make it reappear
- Reboot
Typically using the Command+Tab app switcher or Force Quit trick are enough to bring the cursor back for most apps, but if it’s consistently missing in a single app you may need to relaunch that app itself. Very rarely the cursor will be missing everywhere, which requires either every single application be quit or the computer to reboot.
This is obviously a bug, which means it’s probably an easy fix for Apple. In fact, it may already be resolved in OS X Mavericks as I have yet to run into it using the developer preview builds of 10.9.


For me I reset my NVRAM and SMC on BigSur on iMac Desktop and it’s all fine now.
My mouse previously would alsways disappear after taking a screenshot on my external 4K display.
Absolutely not rare. I have been experiencing this consistently for the last two days. Thanks to the person who suggested hitting F3. It appears to be the fastest fix and I have to do it about every 5 minutes.
10.14.6 Mojave and it still happens very often – At times, every few minutes. Taking the cursor all the way to the top left and clicking (pretending to open the Apple menu) usually makes it appear or alternatively, shutting the lid and opening also makes it appear. Anyone knows when Apple will fix this long-time issue?
I’ve had this issue intermittently. The easiest way i have found to getting the cursor back is pressing F3. so far it has worked first time every time.
My MacBook Air updated last night, and now I have the invisible cursor … like constantly. But I also own an old iMac, and this has been a problem on that computer for a long time. Less frequent than today’s issue, but it’s been going on for about a year. I direct my invisible cursor arrow up to the apple and click and then it comes back. But I’ve done it about 30 times today. Super annoying. And this is certainly not rare or unusual. Apple’s been slacking off on their commitment to make hardware that’s easy for non-techies to use. That used to be their thing. Grrr.
I have this same issue after an overnight update on my 2012 MacBook Pro. I have had my machine and taken immaculate care of it for the last 8 years to never once experience this problem. I’ve noticed any time that the cursor is engaged (hovering over something that can be clicked, or when it changes to that wierd I symbol when hovering over a editable text box, or sitting on top of an app icon in the app dock) and then I try to do ANY type of multiple finger gesture, the cursor disappears. Very, reliably repeatable so this has to be where the issue is happening.
My easiest fix is the use the 3 finger swipe up for app expose and then swipe back down and the mouse comes back. Four finger pinch to open available applications window works too.
I’m having this problem on a minute by minute basis. Swiping between screens seems to cause it, as well as changing apps. The only way I can get it back quickly is to run the cursor up to the top so the menu shows and clicking in that space. It does not have to be on a menu item, just in the space. I have my cursor back until I swap full screens or between apps. Sorry if this has been stated already. I was not going to take the time to read all of the responses. I hope the solution is coming but in the mean time, try this trick.
Ive found if I right click the mouse it comes back?
i found that holding right click and swiping right works
Same problem, Disappearing pointer.
As per the others the problem is increasing in frequency.
Using Chrome almost guarantees the disappearance.
Are any correspondents here in touch with Apple?
I did read to SWIPE UP WITH 3 FINGERS TO GET THE CURSOR BACK. We have a new MacBook pro, and this is the same issue for us. open up a single new window and poof, gone. Is obviously a glitch in the system. I’ve read it is a ram issue, but happens when nothing is open, so not my issue. It works for me, but really Apple it looks like people are complaining for years about this. I have a Mac, and a Macbook pro. Unhappy with both. Won’t by another Apple computer or phone.
Not only is this not rare, it’s not random either. After a recent spring update, both my dad and I are experiencing this on our MacBooks every time we use three fingers to switch between the windows. You have to then drag the invisible cursor to the top of the screen and click, then it appears. This article didn’t help me at all.
This is the exact problem I have as well. Brand new mac air
Precisely the same situation here
Same over here, but not only with using three fingers
I found that moving the “invisible” cursor to the top of the screen, and tapping on the menu Apple bar brings the cursor back into view. This has worked with all application, yes it happens with everything, even virtual desktop. I’m using an older MPB with OSX 10.13
My Macbook Pro has the exact same issues described in this reply thread. Yes, the mouse comes back when right clicking. Yes, the mouse comes back when clicking on the top of the screen. No, it’s not acceptable that this happens minute by minute! And whether or not performing the right actions to get my mouse back, I’m pissed and, yes, occasionally screaming at the computer! No, it’s not acceptable that a fix hasn’t been made for well over a year!
Having the same issue here on a brand new MacBook Air 2019
I have also found a sure fire way to make the pointer disappear – if you’re using the Pages App – drawing shapes, filling them with color – click the ‘color picker’ eye dropper tool – find the color you wish to match – ‘click’ – – Boom-POOF! Boom – the color does change correctly… but then – POOF!! – see ya, bye, later – that pointer is history – it be gooonnnne!
I have tried many times now – turning mouse off, back on … click click click here…. there…. everywhere … I tried walking away and seeing if after time it would come back …. negative.
My solution? I keep my travel plug-em in rolly mouse close by and plugged in …. when the pointer disappears – it does take like 3 or 4 clicks for the plug-em in mousie to be seen – but part of that clicking is my waking sleeping beauty up – so there’s that.
Couple clicks and I keep on rockin …. better than having a stroke while yelling at my computer to bring my pointer back and stop stealing it. If anyone would hear me yelling – (they can’t, though!) they would think I’m probably about to murder some dude name “pointer”. lol — this is usually where my radio will also have someone saying … “Alexa” – and my ‘brat box’ is constantly reminding me that she’s sorry and can’t help with that one. Some days I really feel like I’m a character in someone else’s video game somewhere! Cheers all!
Oh you made me laugh!! You just described me right now!!! I’m not using pages, but just trying to find a gift for my husband’s 60th birthday! A sweet and loving thing to do and I still get punished by the mouse God! This happen to me on a daily basis regardless of what area I’m in.
Thanks for the laugh!
honestly going to the top doesn’t work for me I just have to click frantically until it decides to reappear…
as to the article I think its for people who can’t see the cursor…
Going to the top is the only thing that works for me. This problem just started about a week ago (August 2020). Was it part of an update?
Thanks J.! Did exactly what you said & my cursor has reappeared Shazam!!
It’s called POINTER by the way. You’re welcome.
It’s a disappearing cursor, though if you want to wonder why your Mac pointer disappeared you will find the situation the same and the solution the same too. Glad it helped solve your problem and you found your cursor, or pointer, again.
Nah, it’s called a cursor.
You might be right, but Apple calls it a “Cursor”.
Migth someting like ‘trash’ vs ‘bin, american vs british english.
Check
‘Display’ in ‘Accessibility’, on my computer when a change the ‘Cursor size’ my pointer changes size. So is it ‘pointer’?
I have this issue and thought maybe there was a non-hack to fix it, but it looks like there is not. I personally find the easiest way to get the mouse back is just to go to the top nav bar on the screen and click. Seems to be the fastest and most reliable way IMO. Cheers
Have you found a way to resolve the problem entirely? Ive been using this same method to fix it.
mine has recently just been disappearing and I have done everything I can to get it back, I then tried the clicking at top of nav bar and it works, but I need a permanent solution. Its quite frustrating
Going to the top is the only thing that works for me. This problem just started about a week ago (August 2020). Was it part of an update?
thx, simpliest workaround at the moment
I consistently lose the mouse each time I use Apple collorpicker in Photoshop.
Can’t be bothered to read the whole thread but if I move the imaginary cursor to the top left and click near the apple symbol it’ll reappear every time. Any way to stop it though?
“Can’t be bothered to read the whole thread but”
LOL! Why didn’t you read the article? It talks about figuring out disappearing cursors on the Mac.
The first 2 methods didn’t work for me, the 3rd and 5th were undesirable, and the 4th is too hard.
Joe McVey’s option was easy and worked.
Thanks, Joe McVey~
the cursor keeps disappearing …. have to bring my laptop down and open it back up and there is the cursor.
Just like my Apple TV dying when the new one came out lol!
I have the same question! Thanks!
the easiest and quickest fix that i have found is to just click F3 and the cursor will reappear, after that you can just click on whatever browser you’re on and all is well. F3 is the button that exposes all the windows you have open and its a 2 second fix!
Yep, thats what I do! and it works every time.
My cursor started disappearing from my Macbook Air in the way described. Highly annoying. Scrolled through all the responses here and found to my delight the easiest solution is to close the laptop and open it up again. Cursor reappears as if nothing had happened. Brilliant!
My only solution so far is to drag what would be the cursor to the top left hand corner of the screen and click (near the apple symbol). WTF this is happening is beyond me, I really expect better from Apple, smh.
Yes, If you move the “invisible” pointer to the top of the screen and click, it will reappear… I have the same problem since I updated the OS to High Sierra… it is really annoying. I think this is the last appl product that I bought!
On Macbooks, you can also use three fingers and swipe up to see all of your open apps, click the one you want, and the cursor will reappear.
Closing the macbook and reopening worked for me awhile… then didn’t.
The answer is to scroll your invisible mouse to the top left of the screen (up, up up, left, left, left – to the apple icon) and click. It comes back!
This works on the macbook and the iMac.
actually i tried just clicking the apple and it works im really strugling tho and i cant live like this. I want this to be solved forever. not temporarely
I am running Mojave 10.14.6. Apple wants me to update to Catalina but I won’t because I will lose my old Word app which I still want. Does anyone know if the issue has been resolved with Catalina?
Apple does things that often times cause problems. They say its because they are improving something and it had adverse effects on older equipment but we all know deep down inside that they want you to get a new computer.
What makes me mad is that I have a brand new MacBook pro and this sh*t happens. It may be a minor issue but if I buy a $2k laptop, it better not have some stupid malfunction on a damn mouse cursor. Smh Apple.
I never would shut my computer down and the one day I did it did an update and now it’s giving me problems! Cursor is there but seems like computer froze now! Does anyone know how to fix it! The tips at the top worked once but it happened again can’t get it to work!
Thanks for the tip mate.
This has just started happening to me past couple of days. I usually just sleep my Macbook Pro rather than shut down every time. When I open up for the day the cursor is invisible and I have to keep moving it around to see where it is etc. It reappears after a couple of minutes but so annoying.
the same things happened to me since the last update
Yeah same!! Its so annoying :/
uuugghhh same here
Yep, same here. Drives my nuts.
This has just started happening for me also, after installing the latest update. Very frustrating, and not what I expect from Apple.
Same here. It’s happened ever since my OS updated. I’ve found that I can reliably cause it by putting the pointer over an app on my desktop and using gestures to swipe between full-screen applications. Works every time to cause the bug. A fix that I’ve found is to use that same gesture to navigate to the dashboard and then move the pointer and it will re-appear.
I am running a 2012 MacBook Pro running Mojave. I found this thread due to my cursor disappearing in a variety of fashions after a recent update. I have found this problem to be directly repicable EVERY single time I try and do what BZ states. If I have my cursor located on something in my app dock (not clicking, just hovering to where you can see the app label or the app get big if you have magnification on), and then I try to three-finger swipe to a full-screen app the cursor disappears. This happens in a variety of circumstances as well but, as stated, this issue can be replicated every time I try doing what I described above.
Easiest solutions (try one at a time):
1. three finger swipe up for app expose, then swipe back down
2. four finger pinch to display apps, then swipe back out
3. Essentially any task that involves a motion gesture EXCLUDING scrolling, fullscreen app switching, and switching apps using the app dock should work.
It happens to me every time I open my MacBook Pro. I’m running OS 10.13.6. If I hit F3 to show the open windows it reappears.
The same happens to me. I found out that if you click at the menu bar the cursor will appear. However, I did not find a way to stop it from disappear.
This has started ti happen to me in the last week too, probably due to an update. Very annoying.
I have not done the lasted OS update and this just started happening to me recently. Will probably shut down completely and see if that makes a difference. One additional note, it also started happening on my work computer recently, too, and I didn’t update that one either. Weird!
SAME HERE!!
God damn apple, they must have screwed something over for the latest update
every time I open an app on my dashboard my mouse disappears. I found that every time it disappears I can just put my mouse at the top of the screen to make that thing drop down where you can see the time, wifi signal, and the date. if I just click in that grey area my mouse will 100% of the time come back. it is rather annoying
yes like why did it start disappearing in the first place the only thing I know what to do is bring the mouse to the top of the screen to drop down the options and the mouse comes back for a while and disappears again, like what is up apple. fix it
That is none sense!!!!!
This problem happens everyday with me and so far Apple hasnt solve it.! We only have tricks to get the cursor back but there is no patch that can solve this problem!!!
does anyone know if there is a way to stop the mouse from disappearing overall, it happens to me constantly.
>This is obviously a bug, which means it’s probably an easy fix for Apple.
>6 years, bug still appears.
I have been getting this issue just recently, don’t know when it started but it’s within this week. Whenever I switched tabs, changed pages, typed text, opened apps the cursor would disappear.
my solution at the time was spam right click until it came back somewhere randomly
then I updated my Chrome and it became fixed again I don’t know if this help solve peoples problems, I also killed all the apps I had on in the background
But it still acts the same if I open up Hearthstone(game).
Apple, still happens on Mojave 10.14.3 so PLEASE fix the damn problem! idjiots
Hi Rich,
Sorry to bother you.
Out of curiosity
How long since you purchased yours, was it new?
And if so, how long after you unwrapped it did it first occur?
I’ve never replied to anyone like this but I too am a long, long time sufferer of this Crazy issue and because your comment is so recent and get this, one and a half minutes after Mojave came in last year my cursor vanished and after ages I had to restart like normal… for me.
Oh, what are you using? I’m on my third consecutive MBP in 6 years straight with this nightmare. And No, never ever used Time Machine.
Joseph
Still happens on Mojave, reboot was the only solution that worked for me.
Hi Joseph,
Sorry to bother you.
Out of curiosity
How long since you purchased yours, was it new?
And if so, how long after you unwrapped it did it first occur?
I’ve never replied to anyone like this but I too am a long, long time sufferer of this Crazy issue and because your comment is so recent and get this, one and a half minutes after Mojave came in last year my cursor vanished and after ages I had to restart like normal… for me.
Oh, what are you using? I’m on my third consecutive MBP in 6 years straight with this nightmare. And No, never ever used Time Machine.
Joseph
This article is almost 6 years old and this bug is still happening. CMD+Tab has always worked as the proper fix for me. (I should note that I, too, am using multiple monitors)
Thanks for the tip, the force quit option worked!
An easy fix to keep working on a laptop is to close the laptop for a moment then open it back up. The cursor appears again.
And it doesn’t matter how many programs are open or memory.
Apple, fix the damn problem-
When my cursor disappears, I close the computer, then open it back up. The cursor reappears. This is still a pain, though.
An easy solution I’ve found is to simply click the top of the screen, anywhere on the apple bar, and my mouse will immediately return.
this works for me, it just started happening a week ago, and I found if I send the mouse to the top left over the apple it shows up, it can disappear again a minute later, but now I know how to get it back each time.
I never had this problem until I just upgraded to High Sierra … so seeing this as the top hit when I googled the problem does not inspire confidence … I guess I had enough ram to not see the problem before upgrading, but now it’s happening 3 or 4 times a day, but only when I do fast mouse moves on the track pad, the cursor comes back if I do anything outside of the app that is running, hit the dock, menubar, show all windows gesture etc.
This has been a long standing problem …
I used to contract for Apple as a AQ Engineer and I wrote a bug about this back in 2008 … their ‘fix’ was to make it so the cursor quadruples in size when you shake your mouse vigorously … REALLY? … wow, thanks, in 10 years that is the best solution you could deliver???
If someone doesn’t want to mess with keyboard and cmd-tab: in muiti-screen configuration it fixes with moving the cursor into another screen (so it becomes visible immediately) and then just clicking anywhere. Otherwise returning to the original screen hides the cursor back.
Me too, running into the same issue, on my all new 2018 MBPR13, running 10.13.6. I do, however, have multiple monitors.
It is utter crap to see that this has not been resolved yet.
Yup, me too, and yes, low memory and lots of open Chrome tabs. About every half hour. Close my MacBook lid, immediately reopen and the cursor is visible again. No mouse, just trackpad, and High Sierra 10.13.4
wowza this is 5 years old, still happening, CONSTANTLY. Mostly occurs when moving to a new app (Sketch to Chrome for instance) which is open on a different monitor.
hitting cmd+tab twice instantly fixes it but man it’s so annoying.
Ah – now I’m finding that I have to close other apps as well – very annoying!
Helpful – This has occurred for me for the first time after many years of using Word for Mac. I’m finding that closing Adobe Acrobat Reader solves the problem!
But it re-occurs when I re-open that.
I’m on High Sierra 10.13.3
I have found that closing and reopening the MacBook makes it reappear.
Yes, I have this problem using Excel with Macros. The Macros make the cursor dissapear. Latest version of OS to date.
Just to let you know that I’ve recently purchased a MacBook Air a month ago and have begun to experience this issue since last night.
For folks wishing to troubleshoot I have the following information to share;
1. Software is up to date to 10.13
2. I have a lot of disk space and memory …. haven’t loaded any data from my previous laptop yet
3. The short term solutions given here such as cmd+opt+esc to force shut work but only for a while and then I need to do it all over again
4. I observed this issue over a long sleep mode
Hope something positive comes out soon to eradicate this issue
Thank you all for posting your comments here. its been helpful to read through them
I confirm. I still have that problem. I first thought it was because of VMWare, since I just transited from Windows to Mac, but it seems to be a more general MacOs problem. Very shameful of Apple, who puts all his efforts in appearance, to have own of its most important components to disappear on a regular basis. And even worse, Windows and Linux based system always managed to display the cursor, even when everything else crashed.
Ha ha…
Typical of Apple… it’s 2018 and we still have this problem. In fact there are many software problems with the cursor other than this. The easiest way to get the cursor to reappear in this particular situation is to move the mouse to the menu bar, and just press the mouse. It reappears.
Welp, I know this is an old thread, but just to keep the story alive, this just happened to me on the latest version of MacOS High Sierra (10.13.3) — so this is still a subtle bug. The Command-Tab trick worked for me.
I am using XQuartz to display X11 clients from UNIX VMs running inside of Virtual Box on my iMac mini. I know that’s an atypical use case — and that’s when my pointer disappeared. Just thought I’d mention it in case anyone else is doing the same thing.
Cheers.
Hi, just updating bc this just happened to me on a macbook pro.
All i needed to do was close the lid and put it to sleep and when I opened the lid the mouse was back.
Perhaps on an imac, going to sleep and restarting will also help.
Please reply to email below…
thanks!
My curser disappeared. I have shut down, when opening the curser is on the screen where my symbol and name appears and I put my password. Once entering my password the new gray screen shows my name and bar loading, after loading, cursor is gone and can not click on my symbol above my name to open. I have even let the battery run down then plug in and reastart again. I have tried command,alt tab… everything for problem solving on line! Please help me !
I fing hate Tim Cook.
The mac quality has gone down hill since idiot Tim Cook took over.
I can hardly wait until Apple / someone gets rid of him!
Thank you Kerry – hitting F3 does it! I have had this bug consistently for *years* and the way I was getting the cursor back was quitting an application (any application will do) but that meant I was constantly having to check that I had a application that I could quit.
Uncheck Smoothing and Zooming under “Accessibility” in Sys Prefs.
Found the Zoom suggestion above (mine was disabled), however smoothing was enabled.
Disabling smoothing seems to have helped.
Hope this helps a few folks!
I have the same problem. I have OS X el Capitan and what works for me is pressing the F3 key, the cursor reappears immediately.
Thank you! It works again!
Well…. It’s Been Happening To Me To, but While Only Playing Video Games :/ If your playing a steam game do shift + tab, then do command + tab, and click on something. This worked for me!
Happened again today, March 12, 2017. None of the suggestions worked, I had to reboot and lost work (posting on-line, I’ll survive). So frustrating.
Thank you!!
Try moving the mouse forward/upwards and to the left to get the mouse to the upper left corner of the screen, double-click, with either left or right mouse buttons. Works. (Single click will raise the Apple menu, second click closes the menu). If you have mouse-acceleration on, a fairly quick up-left diagonal movement will be your best assurance of the cursor being firmly in the upper left corner when you stop.
Works for me like a charm.
Similarly, I find moving the mouse forward so the invisible cursor will be anywhere in the menu bar, then clicking, makes the cursor reappear. (Using the color picker eyedropper always causes the cursor to vanish in El Cap and Sierra, in my experience.)
I purchased pro on Nov 26th 2016. From day 1 itself I have been facing this problem. Really irritating. Can someone help me how to resolve this permanently?
Mine is mia upon powering up the computer. Only fix that works for me is powering off & back on until it appears. Never had this issue with my old iMac, circa 2007.
problem persists today as at 23 November 2016 in OSX Sierra.
thought it was me, drives me nuts.
I wiggle the mouse and click randomly until it reappears – with random results of course.
real pain.
I’ve found that if I right click it shows up again
My experience …
To replicate:
1) Open 2 Yosemite windows – resize so both share screen
2) First window run an Flash API (e.g., online TV)
3) Second window – double tap screen to ZOOM in
Cursor will disappears when pointing at first window
To remedy:
Command-Tab
(Mouse re-appears)
the bug still happening in Sierra
Turn off zooming in the accessibility menu
I’m using macbook with external monitor. I just closed the macbook screen and cursor came back. 3 second solution.
hey, you can just ‘double click’ / clock with two fingers,it reappears
Could it be Key logging?
No, the disappearing mouse cursor is a bug on the Mac. It is very unlikely to have a keylogger on a Mac unless you install a lot of sketchy apps from sketchy sources.
Apple hardware is a marvel; its software demands vulgarity to describe it.
Namaste and care,
mhikl
Same thing happens on start up, no cursor. I have found if I put my macbook to sleep with the power button and then wake it up the cursor re appears.
Just lost cursor.completely no tricks.working have presentation.I.can’t lose any ideas
Dual Monitor Mac OS 10.10.4
Cntl+Tab worked like a charm.
Thanks!
*Command+Tab
Says MacGuy… :-D
Thank you!!!
Very, very anoying bug … for years now. It happens using the color picker (icon) in any color palette, mostly the default, Apple’s. As a webdeveloper that’s one of the most used tools on my MBP.
The four fingers up and down on the touchpad is elegant and fast. Most of the time I’m using the fn key (2x) which brings up mission control (program windows). Also elegant and very fast if you have your left hand free … :)
It happens all the time in El Capitan 10.11.3 as well. I do not think Apple has the brain power to fix this problem. It has nothing obvious to do with memory or screens as it happens either way. It does seem related to plug-in active in web browsers (esp. Flash in Safari), but it also happens when (just happened now while writing here) using Apple Remote Desktop and changing between remote computer and your own. Easiest way to get the cursor back is like always to go up to the top of the screen and click one of the menus there.
This has something to do with Flash (youtube player for example, hides your mouse when you’re playing videos) and the mouse somehow gets “lost”/stuck in the flash plugin (invisible)
CMD+Tab indeed, I’ve used a mac for ages and I just did a fresh install of Lion (the reason; frequently used apps+plugins not supported in newer OSs)
and I’ve never seen this before, my strongest guess it’s got something to do with Flash…
Yes this is my experience too, that Flash triggers it. (MacBook Air early 2015, OS X 10.11.6, Safari)
It’s been years and still this bug…
For me, it mainly happens when playing silverlight videos using Safari. Using Chrome instead of Safari seems to do the trick.
I have 20 gb of ram using a 2011 imac 27″ multiple monitors running el capitan and it happens during all my graphic apps everytime i try to change a colour, its feb 2016 and Apple have still not fixed this, very annoying.
Move your cursor into the very upper left corner of the screen and click. The Apple menu dropdown should appear along with your mouse.
I do this regularly on a handful of different Macs and Macbooks as it happens to me daily, especially while using Synergy.
Hope this helps somebody!
This bug continues unabashedly in El Capitan. I usually invoke a four finger swipe (up or down) to get the cursor back in a snap. However, this bug has been following me at least since Yosemite (perhaps even Mavericks). It’s been around for far too long, needless to say.
“visit the dock” and back up works every time
Thanks! The cursor disappeared on my old MacBook Pro with an extra screen. I closed a bunch of open tabs in Firefox and my cursor reappeared without even having to close or restart anything. I’ll try the “visit the dock” trick next time, though.
I am on an older system, 10.8.3 2.6ghz Core i7 (2012/13 ? Macbook Pro) 8gig ram, and have always had this problem. Always while using Firefox (35.0.1)
Happens to me all the time, I just scroll down to the dock and it reappears. for a while.
Not one of these ideas worked for me. Decided to close my laptop and walk away. Came back and mouse returned miraculously! Whew!
I’ve been having the same issue with the mouse lately and I finally decided to look it up. Glad I’m not the only one, but I can’t believe apple can’t find the fix for this. Don’t worry apple when I get my degree I’ll get a job there find a fix.
I’ve been troubled with this for the first time since about a week ago. Never had a problem with Mavericks but now I’m on Yosemite 10.10.5 which is the latest I believe. Wasn’t there an update very recently?
To ‘solve’ it, I just wait patiently for a few minutes and it comes back out of hiding.
I solve it always by doing a right click(Click two fingers at the same time) and it comes back.
The mouse disappearing still regularly happens on OSX. I’m running the latest and the greatest and it still happens :-(
That said, I’ve found it often happens when I have Safari running, particularly when somewhere on a page in some tab there’s a (Flash) video. When playing video full screen it’s normal (and wanted) behavior for the mouse cursor to disappear. Apparently this behavior also sometimes gets triggered when it shouldn’t.
Happens to iMac 27″ 2012 from time to time. I don’t run Chrome, I don’t have more than one monitor, and I’m not using any memory-hungry programs. I thought it was just me but looks like it’s a widespread issue.
Thankyou!!!
This happens to me constantly. If I blindly navigate up to the menu and click it reappears.
One fool-proof way I’ve been able to solve this issue is simply moving the cursor to reveal your dock. Hope it helps.
I have the problem regularly on Yosemite with an iMac 5k.
In fact it seems to happen when the cursor has to change (wait ball or else) and back to normal, but instead of changing, it disappears.
As I use two monitors, a simple clic in the second monitor, but on another application than the current one, brings it back.
Really annoying.
I just had a couple of times where this was a problem. Have had it in the past, always with an open FireFox session. The first time I was able to get the cursor to reappear by closing a couple of applications (cmd-Tab; cmd-Q). The second time I got the cursor to reappear with left-click. That will now be my first option, if it recurs.
Cursor disappears on my new 27″ iMac 3.2 24GB memory!! With nothing showing any sluggishness. It also does this on my 21 inch mac. On both the command+tab trick has always worked. And yes I tend to run a gazillion tabs…my bad
April 9th 2015 @ 7:37AM.. I’m midway thru a photoshop project and BOOM! Cursor disappeared! So, I whipped out the iPhone 6+ and googled the problem and found this article. The “Command+Tab” function worked like a charm. I’m using a MacBook Pro OS X Yosemite (Mid 2014).
I’ve noticed it happens for me when I’m using an app that is SUPPOSED to make the cursor disappear, such as a fullscreen video player. Sometimes I’ll leave put my Mac to sleep when in fullscreen playback mode (no menu or cursor visible) and when I wake it up the next morning everythig is the same including no cursor, except that the cursor doesn’t come back when I move the mouse.
I tried the cursor size trick and it still didn’t bring the cursor back. I quit VLC (video player) and then tried the cursor size trick and it worked. So for me at least the problem seems tied to VLC, or at least apps that make the cursor disappear.
It is pretty sad how Apple’s OS quality has dropped, both Mac and iOS. But it’s still leaps and bounds better than the alternatives.
Thank-you!!!!!!!!!!
This is such a joke- this thread started over 16 MONTHS ago, yet the mouse cursor bug is STILL happening. I love all the tricks and shortcuts listed here- but this is insane! Why do I need a shortcut to find my mouse cursor?!
“This is obviously a bug, which means it’s probably an easy fix for Apple.”
This is such a non sequitur.
Sorry, but none of these tricks or shortcuts from the last two years posted here, nor from other blogs I’ve seen since 2011 is a fix or a valid explanation of why this is happening. I too have a completely updated Mac, running Yosemite, 8G ram, and the mouse still disappears on one of my two dual monitors occasionally. So, anyone who thinks any of the new updates have fixed this is unfortunately wrong. Just wait long enough, and it will happen again. The tricks like “Command+Tab” and bringing up “Force Quit” help, but are nonetheless still only “work-around” solutions. Why Apple takes soooooooo long to fix what seems to be a simple bug is baffling.
There is no explanation for why the cursor disappears other than a bug, and Apple software quality has declined dramatically particularly on the Mac so this is not surprising to see something so small go unfixed for years. OS X Yosemite is basically still in beta.
Most sensible comment on here and emulates my views completely Eric!
Same problem here since moving to Yosemite from Mavericks last week. Never saw it before, but now it happens so much that I’m looking into add-ons/extensions (e.g. mouse locator) to help.
The trick I found to recover is to go to the dashboard. Either do – or just bang around with the invisible mouse until the dashboard shows up.
yes, I am answering myself.
1st – My statement should have said Control + Left Arrow, instead of just “–“.
Also, this issue seems more frequent when I’m leaning back with the macbook’s front edge bearing to weight of the macbook at/near my beltline. The mousepad also tends to be less responsive this way.
This makes me wonder:
– if each unit (or batch of units) has a different susceptibility to what should be inconsequential frame distortion at the trackpad.
– And/or the low-level driver doesn’t distinguish such frame distortion at its edges, as it should.
How is it that this bug hasn’t been fixed yet? This isn’t the only cursor issue, either. It bothers me that the resize cursor rarely appears when the mouse is at a window edge. Also, the hand cursor rarely appears to identify links in a browser.
Same problem here since moving to Yosemite from Mavericks. Usually seems to happen in Firefox but maybe that’s because I use that app the most. I have Mouse Locator installed and it will pop up showing me about where the cursor is, but with no actual cursor in the middle. I’ve just been clicking about blindly until it reappears. The tips here at least give me a few more scientific tricks to get it back. Very annoying.
I’m completely baffled by this. I have three MacBooks that have been through various versions of Mac OS X (including the latest 10.9.5) and I have never had this issue on any of them.
My husband and brother-in-law experience it frequently on their MacBooks (same model and same OS).
Not to defend Apple, but it’s possible the root cause of the issue isn’t as easy to track down as some folks suggest.
I don’t use Firefox (or several of the other apps people mentioned). I do use Safari and Chrome.
This can happen many times in a day for me. I have many applications open and multiple monitors.
All I have to do is click somewhere else and then the cursor returns. For example, the disappears most often inside a Java application. If I move the cursor outside of the Java application it re-appears. Then I click anywhere and move back into the Java application and it’s fine.
Moving to another application and then back isn’t enough. I have to move out of the application and then click.
I have had this issue for a while now and never really looked into it because i thought it was just my computer. All the answers to fix it seem very complicated, but i found out if i quickly drag it down to the dock and then quickly drag it back up, it reappears.
Happened to me at least three times in the last few days, on Mac Pro ‘black jar edition’ with 3 monitors connected, cursor disappears on the biggest in terms of resolution, 2 smaller are fine. OS X 10.10.1 Yosemite
It’s not fixed in Yosemite either. Perfect pain.
Occasionally it sorts itself once I quit from Safari. Mostly I end up shutting down and restarting. It does seem to happen when I’ve multiple apps running (but that’s always, that’s the point of using this Macbook Pro) and when I haven’t done a restart for a while.
I’m experiencing this again frequently after not having it happen in probably ~9 years. My solution has always been to click directly on the desktop and drag, (as if you were to be selecting a group of icons) then release. Cursor always reappears immediately after that.
WOW!
I just upgraded an from my old 32bit iMac to a new MBP with 16g ram and an i core 7 processor, only to discover that my brand new $3K laptop can’t even provide me with a functional mouse!!!
Worst still, i now read apple has been aware of the problem for over 12mths and it STILL not fixed.
I upgraded because i finally tired of all the glitchy crash causing bugs that my iMac had developed.
Looks like that might have been a $3K mistake. The 2 $800 PC’s i bought for my kids seem to function perfectly.
Seriously considering taking this MBP back and exchanging it for one of those, now.
Would never have happened when SJ was alive and in charge. Apple has really lost its way since he left this earth!
To use a Mouse on your Mac connect it with a USB cable and move it around on a desk to see hte cursor appear on your screen. Clicking the button on the mouse where the little arrow is (that’s called a cursor) will activate that screen item. Your Windows PC will also use a mouse cursor, it’s not just a Mac thing.
If Apple spent half as much time on functionality as on appearance, it would make awesome products. Alas. This happens to me in Firefox all the time, so I have a hot key that will get me to my desktop screen, I click the cursor, and then I return to whatever I was doing. Annoying, for sure, but it’s a much better option than force closing apps and rebooting!
I have Yosemite and have tried every workaround. Nothing works. Had the same problem with Mountain Lion and Mavericks.
I even repaired the desktop with DiskWarrior and repaired permissions with DiskUtility.
The two programs I notice the most problems with are YouTube and a jigsaw program I use.
I use two screens. I find taping on the blank one brings the cursor back.
I was a diehard Safari user until I met Yosemite. It’s frozen. It must’ve watched the movie two often and caught a cold. I’m now an Opera fan and wondered why I stopped using this marvelous browser.
A frustrating problem which Apple needs to fix.
This is still an issue for me with Yosemite.
My workaround is to enable temporary zoom. System Preferences -> Accessibility -> Zoom -> More Options button, and check “Enable temporary zoom”. Then simply hitting Ctrl+Option brings back the mouse cursor.
I recently switched to Mac(Thank God) and encountered this issue.. i started off directly with Yosemite…so idk much about the previous versions, but yes i face this problem quite frequently.
I mostly work on Chrome, so till now that where i have experienced this, but i am sure it would be happening for other third-party apps and softwares too.
Switching the windows(Command+Tab) always brings it back for me..so thats the fastest work-around i believe we have for now.
Hope Apple fixes this once and for all…
I’ve been using Macs for 20 years and I’ve had this disappearing cursor happen ever since I’ve been using photoshop regardless of OS. I’m in Mavericks now but it was happening in Leopard and Snow Leopard and even before that. If you click off the app giving you issues it should reappear, I usually click on Safari and then back to PS and the cursor is there. In my case it’s only Photoshop that causes this and usually only when I initially open the app. After the first time I don’t have an issue for the rest of the time I use it. I have this issue every time I open it. I don’t think Apple will be fixing this any time soon since it’s been going on for years.
Every solution listed above has a common denominator that most people seem to be overlooking. The tricks above, the moving to hot corners and moving to the dock all require that the OS interact with the cursor. Notice that clicking in the application (and sometimes Finder) does not bring back the visibility of the cursor. But clicking on an OS menu will.
My “trick” (that is faster than any other mentioned), is to jam my cursor all the way up to the top of the screen so that it should be located on the menu bar, and click. Invoking a menu click always bring my cursor back.
And I agree with Sandi – rare my butt! I am running two 50 inch 4k monitors on my MacPro and that cursor is hard enough to find even when it is working! This happens way too often. Hoping Yosemite will fix it finally.
Not rare – existed in Mavericks since upgrading and exists in Yosemite. I can hit command tab and back to get the cursor back. But very annoying. Similar problem is losing window focus while in the middle of typing. I keep thinking i hit a key combo, but I think it may be a related bug.
The only thing that worked for me was a restart. Pain in the arse.
Rare my butt.
In my case, it’s Firefox where the cursor vanishes consistently. I can get it back by sloughing off to the edge of the monitor, where (usually) I’ve got a sliver of the desktop showing. Click there, and I’m back in business.
Hey guys,
I have the same problem in Mavericks, and is really annoying when I’m programming in XCode .The faster solution so far for me is just to move the mouse to the top left corner and shake it if is neccesary, then the pointer is back. If not the CMD+TAB is a good solution, in case you want to keep in the same application after the CMD+TAB, just keep pressed both bottons and with the mouse pointer select your actual app again.
See ya!
Awesome. Did #1 and #2 (without having to actually force quit anything) and it worked.
How does one launch system preferences without a cursor?
Hit Command+Spacebar to bring up Spotlight, then type “System Preferences” and hit return. No mouse required!
Guys this is a simple issue that needs to be adjusted by the programmers.
A missing cursor is mainly due to a lack of feedback code to maintain critical systems… its location or importance in the code needs to be elevated to the same level of memory allocation as things like the playback buttons.
For example if there are 10 levels of memory allocation within a computer. A one is the lowest needed items… something rarely used & stored in the HDD & a 10 would be things used every day all the time, mission critical systems like the display or the playback buttons.
Thats my $0.02 but computers are not as complicated as people want you to believe.
My cursor disappears each time I boot up my MacBook Pro running Mavericks. By accident I discovered that if I do a three-finger swipe to the right on my Trackpad (so that I get the Widgets screen), wait 3-4 seconds, then do a three-finger swipe to the left to get back to the Finder, the cursor suddenly reappears!
When this happen to me, I just press F9 or F10and then the mouse reappears.
Still a problem with Mavericks 10.9.4
It’s pathetic that Apple continues to leave this bug unfixed through many OS releases.
Thanks Jarik,
even with no hot corners configured, opening Mission Control (even if you close it right away) seems to restore the missing cursor.
Yes, swiping up with 4 finger gesture to launch Mission Control (set in System Preferences > Trackpad) will reveal the cursor.
Thank you that worked (the first one)… love the internet with all the friendly helpful people…. you all rock
I am having the same problems. This is really frustrating! my old 2009 MBP was not troubles at all, now buying a new macbook air with maverick the mouse is disappearing all time time!
come on apple – fix it!!
TIP #1,162 – Works every time for me.
When the mouse cursor goes invisible, scroll blindly to/past your dock (at the bottom of the screen), then then back up again. It will appear.
This works every time for me. As soon as you begin to scroll up again, it should appear. I was hoping things would change in Mavericks, but I believe it goes invisible more. I just came to the forum to see if anyone had the full proof solution, but what I’ve been doing seems to be the easier of all I just read.
Good luck.
This solution works for me most every time.
Happens to me constantly- more frequently when I am streaming something or there is a form of Flash running- it seems to be an error that occurs while running 3rd party apps or plugins. The Mac OS has just fallen apart due to whatever background processes run now. Don’t be so naive as to think you can expose them all, either. Please don’t insult my intelligence with any ‘YU so paranoid’ responses. I have things complete fail to respond and then take me back to login- a lovely way to gain access and implement changes. I wish they would at least provide a sense of false confidence!
This problem is at its worst in PDFs and WORD in text that is in italics – it appears and disappears as you enter/leave such text. This has been going on for over a year, well before Mavericks.
Incredibly annoying when you need to select a phrase of a few sentences.
how change color Mouse Cursor?
My Macbook Pro is running 10.8.5 and the disappearing pointer problem has been increasing in frequency. A couple of months ago it happened once every couple of weeks – now it is daily or several times a day. Mostly happens to me when using Firefox.
Frustrating!!
We recently replaced a worn out wireless Magic Mouse with a wired one and started having this problem. We’re using Mountain Lion. Called the Apple repair shop who sold us the new mouse and he suggested we replace our colorful mousepad with a solid color one. Problem gone.
But no consolation on an air book where it happens all the time, too.
I’m having the same problem, I’m using a solid colored mouse and the pointer is disappearing and the top gray menu bar opens then rotates to the left. Weird!!
I never had this problem before I bought a new computer with Mavericks installed. It’s a bug in the new system as far as I am concerned. Been using a Mac for 25 years plus, never encountered it before. Thanks Apple! You know about this – how about fixing it!!! This is not what I expect from Apple. Steve must be turning in his grave….
I have found that flipping to a hot corner (a feature of ‘mission control’ previously ‘exposé’ ) tends to restore visibility to your cursor when it disappears. Would be nice if it where fixed. In terms of cause, It seems to happen the most to me in relation to video playing in web browsers. (mousing across the video when focused in another application vanishes the mouse?)
This is exactly what I’ve noticed too. Just a few moments ago the cursor disappeared, I tried the top left hot corner which didn’t work, then the bottom left, and the cursor came back.
It still seems hit or miss as to which one will work.
Thanks for the tip. My mouse disappears quite frequently even in Mavericks and your tips work to get it visible again. Also with Mavericks I am unable to scroll in mail with the magic mouse. Hope Apple fixes this soon. It’s frustrating.
This has not been solved in Mavericks. It happens just as often as before the Mavericks upgrade.
Why doesn’t Apple fix this?
In the mean-time, an app called Moom helps significantly. Although its main purpose is to move the pointer using the keyboard, it also has the ability to map a keyboard shortcut to show the pointer. In so-doing, it also makes the invisible Pointer visible again!
I’ve mapped it to Ctrl-Enter. Whenever I find myself jerking the mouse around trying to get it to appear, a simple Ctrl-Enter displays it.
Just bought Moom but can’t see how to dedicate a shortcut to show the mouse pointer as you suggest. Sorry for being thick! How do you do that, please?
No, it’s not fixed. I never experienced the problem until I installed Mavericks. Now it happens routinely. Most often in Lightroom 5, with which I use dual monitors. But it has also occurred in Safari with multiple windows open.
I have not found a solution. So far I have navigated blind (usually saving work) and shortly the pointer returns. No consistent reason observed yet as to what brings it back.
I just experienced the problem and I’m using Maverick. I doubled-clicked a book in iBooks, and when it launched in Preview (it’s a PDF), the mouse disappeared. Quitting Preview brought it back. I couldn’t duplicate the problem, though.
I take it all back had my pen stood on tablet DOH!
Hi Paul I have downloaded Mavericks and since doing so my mouse regular disappears ,often it does not appear when starting.I have to keep on rebooting computer until its visible on boot up.Other times it just disappears if allowed to sleep.
Hi Paul,
I have exactly the same problem on my Macbook Air, both on Safari 6 and 7 – with both OSX Mavericks and my previous operating system! It’s a rather frequently recurring problem, several times a day at least, and though there are fairly easy workarounds, I find it funny that Apple hasn’t managed to fix it altogether yet.
The cursor disappears regardless of the number of applications open (i.e. there shouldn’t be a low memory problem) and reappears when I CMD+TAB onto finder or any other application than Safari. Sometimes it finally reappears in Safari after a few switches back and forth.
Hi,
I just wanted to update to the comments here because it seems there hasn’t been an update in a while. I’ve been running 10.10.1 and it still happens with multiple monitors!
It’s not a resource issue because I have greater than 8gb ram left and my CPU is less than 10%.
10.10.2 It still is happening. I just got it on a single monitor with more than 9 gigs of unused memory. It goes away easily enough but is very annoying.
and we are on to 10.10.3 and it is still happening.
Plenty of RAM left over, happens on both my 2 monitor set up and work and just using the display on my MacBook Pro (retina).
on Sierra 10.12.6 and it STILL happens hourly
Hi there, had the problem myself (and still have) However I discovered that when I have configured interactive corners on my screen and move into a interactive corner when my mouse disappears, it reappears most of the time by doing so, so no need to restart or other things to click and reset or restart, hope this will be useful to many of you………..
Another way to fix the issue is by moving your mouse cursor to the top left corner and click the apple logo and i will come back up.
this works for me ! the only one of all the options listed above that does. thank you for this !
I have found that if you can invisibly get the cursor up to the very top of the page near the main bar it will reappear. I am using Firefox and Yosemite 10.10.2
I have found that pressing down on the mouse when the cursor is missing and moving it a bit will show you where it is. It makes a highlight line or whatever you call that. Once you know where it is drag it to the dock and the cursor will appear.
For me it was KODI somehow blocking visibility. The cursor was visible in Kodi, but vanished after 2 secs in all apps incl. Finder.
Just setting KODI to shut down gave me the cursor back.
[No other trick helped – not even restart, as OSX reinstated all open apps, and thus brought the problem back)
PS: At present KODI is frozen, but I have my mouse back :-D