How to Set a Firmware Password on a Mac with macOS Mojave, Sierra, OS X El Capitan, Mavericks

Mac users in higher security risk situations may wish to enable an optional firmware password on their machines,which offers an advanced level of protection. In short, a firmware password is a lower level layer of security that is set on the actual Mac logicboards firmware, rather than at the software layer like FileVault encryption or the standard login password. The result of setting an EFI password is that a Mac can not be booted from an external boot volume, single user mode, or target disk mode, and it also prevents resetting of PRAM and the ability to boot into Safe Mode, without logging in through the firmware password first. This effectively prevents a wide variety of methods that could potentially be used to compromise a Mac, and offers exceptional security for users who require such protection.
Important: Like any other essential password, use something memorable but complex, and do not forget a firmware password after it has been set. A lost firmware password is unrecoverable on most modern Macs without a visit to an Apple Store or sending a Mac into Apple Support for service and recovery. Older Mac models may be able to use a hardware intervention method to bypass firmware passwords, but these methods are not possible on new Macs without access to removable batteries or memory modules, thus the visit to Apple.
How to Set a Firmware Password on a Mac
Setting a firmware password is rather simple, though it’s handled slightly differently in macOS Mojave, MacOS High Sierra, MacOS Sierra, OS X El Capitan, OS X Yosemite, and OS X Mavericks than it was in earlier versions of Mac OS X.
- Reboot the Mac, and hold down Command+R to boot directly into Recovery Mode
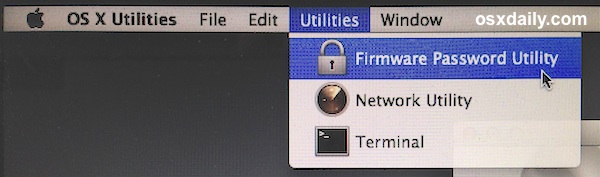
- At the OS X Utilities splash screen, pull down the “Utilities” menu bar and choose “Firmware Password Utility”
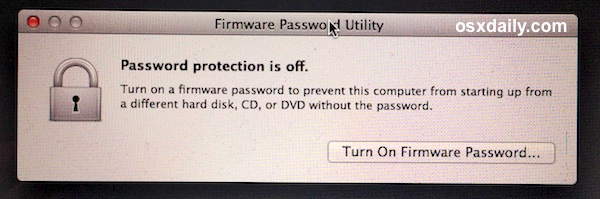
- Choose “Turn On Firmware Password”
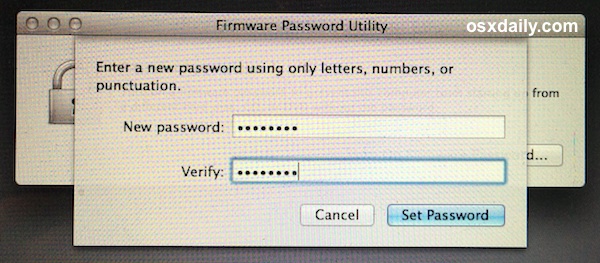
- Enter the password twice to confirm, then choose “Set Password” to assign to assign that password to the Mac – do not forget this password or you may lose access to the Mac
- Choose “Quit Firmware Password Utility” to set the EFI password
With the firmware password set, you can reboot the Mac as usual. For any standard boot or restart, the Mac will boot into macOS X as usual, and go directly to the normal Mac OS X login screen.
When / Where the Firmware Password is Visible on Mac
The firmware password will not appear during a regular restart or boot of the Mac, it only becomes mandatory when the Mac is attempted to boot from alternate methods. This may be in situations where a Mac is attempted to boot from an Mac OS X installer drive, an external boot volume, Recovery Mode, Single User Mode, Verbose Mode, Target Disk Mode, resetting the PRAM, or any other alternative booting approach that will summon the rather plain looking firmware password window. There are no password hints or additional details provided, only a simple lock logo and a text entry screen.
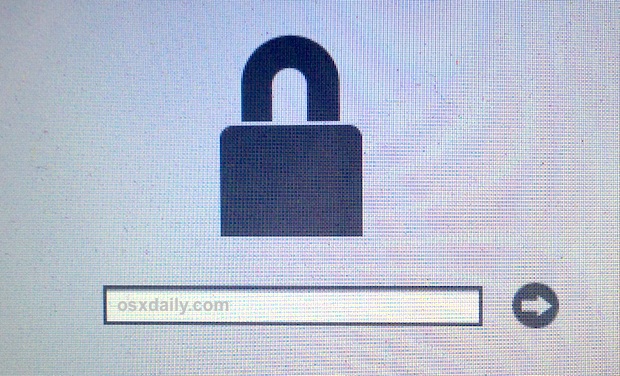
An incorrectly entered firmware password does nothing and offers no indication of login failure except that the Mac won’t boot as anticipated.
Note that all modern Intel-based Macs refer to firmware passwords as EFI (Extensible Firmware Interface) passwords, while older Macs referred to them as Open Firmware. The general concept remains the same, just different hardware.
Should You Use a Firmware Password on Your Mac?
Most Mac users will find a firmware password an unnecessarily heightened security precaution, and using this feature is best limited to Mac users in higher risk environments where having maximum security is a requirement. For the average Mac user, a standard boot login authentication and screen saver password is usually sufficient protection, while enabling FileVault disk encryption can offer additional security benefits to users who want their files and data protected from unauthorized access. FileVault can also be used as a means of preventing manual resetting of account passwords on Macs within higher security risk environments, but as several readers pointed out in the comments, the firmware protection should also be used in high security situations.


I set firmware password by mistake nd when I want enter the firmware paswornd no key enterd in the password logo wt I can do ??
Anyone else having issues with this? Currently my internal drive is encrypted with FileVault2. When I enable the firmware password my mac boots into a screen with a folder and a question mark on it. This means he can’t find the boot drive. I have to forcefully shutdown my Air and reboot while holding the option key. Next I have to enter my firmware PW and select my internal harddrive. Next I need to enter my FileVault PW before it boots.
I would like to use the firmware PW without all the hassle of having to hold down option while booting. Any ideas why my mac can’t find the boot drive when I have the firmware PW enabled?
Thanks!
sounds like you’ve got an issue with the selected boot drive/startup disk. take a look in preferences and see whats set
If you use Remote Desktop I would not recommend using a Firmware password. If the power goes out and comes back on, the Mac will not boot and you will not be able to access it remotely.
I’m wondering how the three types of protection (Account passwords, filevault and firmware password) compare in preventing access to files on a stolen laptop? Without filevault, could a thief remove the drive, place it into an external enclosure and access all files?
Does filevault change the way that time machine backs up, and options to restore files?
Keep in mind that the current version is called FileVault 2, not FileVault and any documentation and/or reviews you read should be for the second version not the first as the two are very different.
I’ve been using FileVault 2, for about 2 years now on my MacBook Pro and don’t even notice it running. I use TimeMachine and restore files from there occasionally without even noticing FileVault 2. The only time I have noticed FileVault 2 is when booting my laptop from an external drive and trying to access my laptop’s internal drive. A popup is displayed that asks for the drives password. I’ve used that once in two years so its very limited.
To learn more check out: http://support.apple.com/kb/HT4790
So, in terms of passwords there’s 4 levels of security that the average consumer can setup; Firmware, FileVault, User account, and Apple ID (for Find my Mac). Personally, I have all but FileVault turned on primarily due to the fact that you need a certain amount of free space on your drive to encrypt and de-encrypt your data, and it can make things run… slow or weirdly. I’m also not too terribly worried if someone were to see the data on my Mac, I don’t keep important or secret docs or data on my computer on purpose, that’s just me though. Lot’s of people have lots of sensitive information so they may need FileVault.
To answer your first question though, without FileVault a thief could remove the drive, place it in an external enclosure and access the data. If you have a user account password, this makes it a little tougher as they’ll need to work around access permissions, but the answer is yes none-the-less. To answer your other question, FileVault can (and I believe by default does) encrypt your backup as well.
Sorry if that was rambling, hope it made sense.
The three types of protection should all be used.
1. The firmware/EFI password makes it difficult for a thief to wipe the internal drive(s) or to boot from an external drive with the goal of reading your data.
2. FileVault 2 makes it difficult for any unauthorized person(s) to read your data, even if they can read the internal drive. I use it on all my machines and have not noticed any difference in speed/responsiveness. The encryption/decryption happens at an extremely low level and is totally transparent to the enduser.
3. Account passwords will prevent casual attackers, drive-by web attacks etc from accessing your data or stealing your keychain.
4. Enable “Find My Mac”. It’s a no brainer.
If you have a laptop all these things are basically essential.
This brings me to another point: you may wish to consider making your keychain password distinct from your login password. (For an added measure of security but also an added inconvenience.)
Finally – don’t forget to encrypt your Time Machine backups (or if you use Carbon Copy Cloner enable FileVault 2 on your clone also).
I would recommend NOT using Find My Mac. If the Mac is lost or stolen and you have enabled FileVault 2 (assuming as always a good password) then your data is safe. If you’ve enabled the EFI password then your Mac cannot be re-imaged.
Therefore the Mac won’t be on the Internet ever again in this situation so Find My Mac will be useless. Find My Mac does not support Activation as it does with iOS devices so there’s no benefit there either. But if your iCloud account was compromised, the attacker could remotely wipe your Mac.
So on balance I keep my Mac off Find My Mac so that in the event of an iCloud account compromise it remains in my control, and it’s encrypted and secured so that in the event of theft it’s useless and the data is safe.
What if you have a guest account enabled? Perhaps the thief would try and access that account. I’m not sure if the Mac would contact iCloud in this situation, however.
I don’t think this is correct. On newer Macbook Pros that have the Power Nap features, the machine may still connect to the internet (and be responsive to Find My Mac) even while asleep. If the machine is stolen while asleep, there’s every reason to believe it will still broadcast its location.
Even for non-Power Nap enabled machines, a thief could connect using the Guest User account and that would be enough for Find My Mac.
Hi, curious about file vault for my home folder. In case I have a hard drive issue so that no one can recover the files. Will file vault or firmware work better?
FileVault encrypts data and is impossible to access without the FileVault password, while Firmware passwords do not offer encryption. If you want to protect your data, use FileVault.
I would suggest that most people use the firmware password, high security situations or not. It’s easy to set up and only gets in the way in rare circumstances, like booting from another drive or the Mac is stolen. For me, it’s a no brainer to go ahead and set up.