Perform Detailed DNS Lookups with host Command in Mac OS X
All domains are associated with an IP address, whether it’s for a website, mail server, or whatever else. While using nslookup offers a simple way to get DNS information and an IP for a specific website or domain, if you want a significantly more detailed retrieval, you can use the host command instead. The host command performs an extensive DNS lookup for whatever domain it’s pointed at, which makes it much more useful than nslookup or dig for many situations. This can be helpful for many situations, whether to troubleshoot and discover DNS propagation issues or simply to get an actual IP address, CNAME, IPv6 address, or otherwise.
How to Perform Detailed DNS Lookup with host from Command Line
Using the host command is quite easy, it’s included in Mac OS X and Linux, so you should be able to use it wherever necessary to do a DNS lookup. Command syntax is simple, open Terminal and just use the following:
host [domain]
You can also use the -a flag to get any DNS details, which winds up providing a comprehensive lookup:
host -a [domain]
For example, replacing [domain] with google and running host -a on google.com gives an extensive listing of DNS lookup details of myriad IP addresses and mail servers.
Air% host -a google.com
Trying "google.com"
;; Truncated, retrying in TCP mode.
Trying "google.com"
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 64673
;; flags: qr rd ra; QUERY: 1, ANSWER: 27, AUTHORITY: 0, ADDITIONAL: 0
;; QUESTION SECTION:
;google.com. IN ANY
;; ANSWER SECTION:
google.com. 299 IN A 1.2.3.208
google.com. 299 IN A 1.2.3.213
google.com. 299 IN A 1.2.3.210
google.com. 299 IN A 1.2.3.212
google.com. 299 IN A 1.2.3.215
google.com. 299 IN A 1.2.3.209
google.com. 299 IN A 1.2.3.214
google.com. 299 IN A 1.2.3.221
google.com. 299 IN A 1.2.3.218
google.com. 299 IN A 1.2.3.211
google.com. 299 IN A 1.2.3.220
google.com. 299 IN A 1.2.3.219
google.com. 299 IN A 1.2.3.216
google.com. 299 IN A 1.2.3.217
google.com. 299 IN A 1.2.3.207
google.com. 21599 IN NS ns3.google.com.
google.com. 599 IN MX 40 alt3.aspmx.l.google.com.
google.com. 21599 IN TYPE257 \# 19 000714981749824711982818926F6D
google.com. 21599 IN SOA ns1.google.com. dns-admin.google.com. 2015031701 7200 1800 1209600 300
google.com. 599 IN MX 50 alt4.aspmx.l.google.com.
google.com. 3599 IN TXT "v=spf1 include:_spf.google.com ip4:21.71.93.70/31 ip4:211.24.93.2/31 ~all"
google.com. 21599 IN NS ns1.google.com.
google.com. 21599 IN NS ns2.google.com.
google.com. 599 IN MX 10 aspmx.l.google.com.
google.com. 599 IN MX 20 alt1.aspmx.l.google.com.
google.com. 21599 IN NS ns4.google.com.
google.com. 599 IN MX 30 alt2.aspmx.l.google.com.
Received 613 bytes from 8.8.8.8#53 in 98 ms
Air%
You'll notice towards the end that the DNS servers used for the lookup will be listed as well, without having to query them directly, though that's still recommended if you want a comprehensive list of all the DNS servers a specific machine is using. If they were changed recently and the data you are seeing does not match what it should, flushing DNS cache can be necessary.
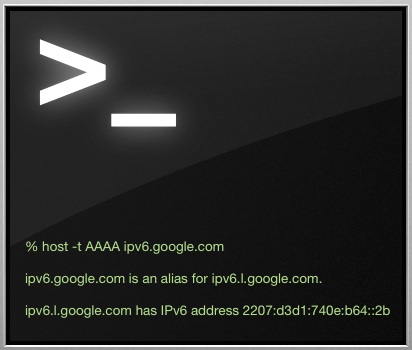
You can also get specific record types with the -t flag, for example, if you want a CNAME or ANAME, or NameServer (NS) record, the syntax would look as follows:
host -t NS [domain]
Again to use google.com as an example, querying the name server would result in:
% host -t NS google.com
google.com name server ns3.google.com.
google.com name server ns2.google.com.
google.com name server ns1.google.com.
google.com name server ns4.google.com.
The next time you're working on DNS issues, remember the host command, it's a good one to add to your networking toolkit.


dig is far more versatile since it is easier to script, has more options, specially +trace
dig
Yes, dig and nslookup are good utilities too. Why do you prefer dig to host?