How to Show & Verify Code Signatures for Apps in Mac OS X
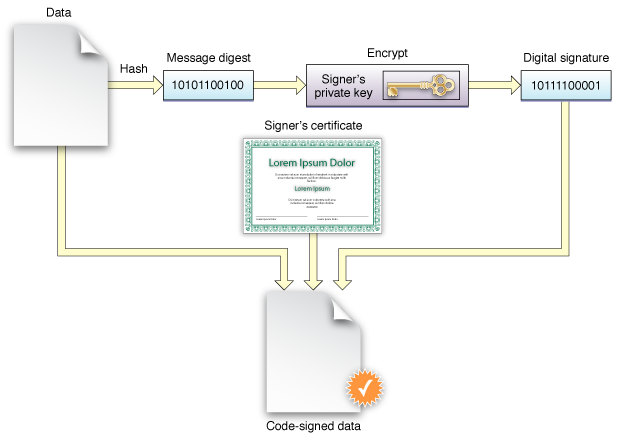
Code signed applications allow security conscious users to verify the creator and hash of a particular app to help confirm it has not been corrupted or tampered with. This is rarely necessary for average Mac users, particularly those who obtain their software from the Mac App Store or other trusted sources since the apps are certified, but verifying the digital signature of an app can be extremely helpful for users who get apps from third party sources.
Verifying a code signature is particularly important for those getting software and installers from p2p and distributed sources, perhaps a torrent site or newsgroups, IRC, public ftp, or another network resource. For a practical example, let’s say a user can’t access the Mac App Store for whatever reason, but needs to download a Mac OS X installer application and thus relies on a third party source. Such a situation is when it would be important to know and verify that the installer has not been tampered with and is legitimately coming from Apple, and aside from checking sha1 hash directly, the easiest way to do that is to check the code signature and cryptographic hash of the app in question.
How to Check Code Signature for Apps on Mac
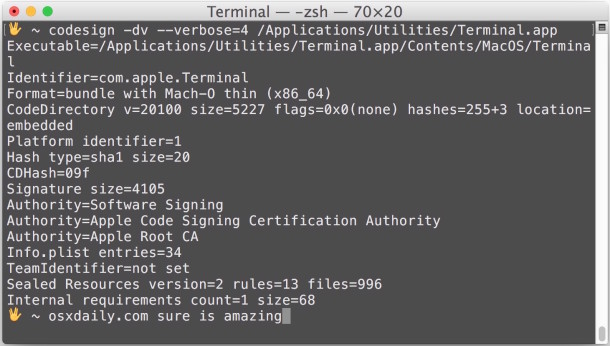
To get started, launch Terminal, found in /Applications/Utilities/. We’ll be using the aptly named ‘codesign’ command, complete with the -dv and –verbose=4 flags to show identifying information about any application, including it’s hash type, hash checksum, and signing authority.
The basic syntax is as follows:
codesign -dv --verbose=4 /Path/To/Application.app
For example, let’s check the signature on Terminal.app, located in /Applications/Utilities/
codesign -dv --verbose=4 /Applications/Utilities/Terminal.app
Executable=/Applications/Utilities/Terminal.app/Contents/MacOS/Terminal
Identifier=com.apple.Terminal
Format=bundle with Mach-O thin (x86_64)
CodeDirectory v=20100 size=5227 flags=0x0(none) hashes=255+3 location=embedded
Platform identifier=1
Hash type=sha1 size=20
CDHash=0941049019f9fa3499333fb5b52b53735b498aed6cde6a23
Signature size=4105
Authority=Software Signing
Authority=Apple Code Signing Certification Authority
Authority=Apple Root CA
Info.plist entries=34
TeamIdentifier=not set
Sealed Resources version=2 rules=13 files=996
Internal requirements count=1 size=68
What you’re looking for are the hash type, hash, and authority entries. In this case the hash type is sha1 and the signed authority is Apple, which is what you’d expect.
Yes, you can also use the command line to just check sha1 or md5 hashes of application installers and downloads and compare them to a legitimate source, but that won’t reveal the code signing and certificate details.
Keep in mind that most code signed software that has been modified by an unauthorized party will be rejected by Gatekeeper in Mac OS X, unless Gatekeeper has been disabled or otherwise circumvented, but even with Gatekeeper left on it’s theoretically possible for an enterprising goon to find a way around it, and of course software that hasn’t been certified by a identified developer can always be launched around Gatekeeper anyway.
You can read more about code signing on Wikipedia and on the Apple Developer guide to code signing here.
Do you ever check if apps are signed? It can be a valid way to determine what some processes and apps are, and also can be helpful for troubleshooting. Give it a try the next time you’re wondering what something is and if it’s signed or not!


Thanks! That worked
You’ll need to run the command against the .app, not the .ipa. unzip the .ipa and then run the command against the .app.
I’m using macOS Monterey; Terminal is moved to `/System/Applications/Utilities` folder.
I’m on Monterey and Terminal.app is in /Applications/Utilities/
Hello,
If I edit files inside a mac *.app, do I have to sign it? It crashes due to codesignature issues.
I deleted the _codesignature folder and the app started working. Is this fine? Would it work on other systems too?
Yes, you need to remove codesignature if you change the app.
Best way is to run codesign –remove-signature $APP_NAME as this way you remove signature from frameworks inside app also.
In the article under “The basic syntax is as follows:”
The syntax is incorrect:
code sign -dv –verbose=4 /Path/To/Application.app
There should be no space between “code” and “sign” as in the above – should be “codesign” which is the executable.
Had me wondering as Microsoft Visual Studio Code has an executable /usr/local/bin/code which ran when I first tried the above command (before noticing the correct one below).
Thanks though for all your articles! Just a typo.
The result I got after run this command was “bundle format unrecognized, invalid, or unsuitable”.
Do you know what this mean?
You’ll need to run the command against the .app, not the .ipa. unzip the .ipa and then run the command against the .app.
Please fix the typo….
“The basic syntax is as follows:
code sign -dv –verbose=4 /Path/To/Application.app
This is incorrect. There is no space between code sign.
The proper command is:
codesign -dv –verbose=4 /Path/To/Application.app
The correct command is used in other areas of the article.
I get many apps from sites for my amateur radio applications and so run into these types of issues. Consequently I haven’t upgraded to El Capitan and I doubt I will.
Using El Captain for my amateur radio apps and have had zero issues. Actually the OS X upgrade has provided a better experience.