Detect Webcam & Microphone Activity on Mac with Oversight

Though Mac users don’t usually have to worry excessively about “camfecting” malware and spyware, some security conscious users may find it nice to know if a process or application is attempting to access their computers web camera or microphone.
With the help of a free third party security utility called Oversight, you can have your Mac alert you anytime an application or process tries to activate either recording device on the computer.
The developer of Oversight explains why a tool like Oversight could be valuable to some users:
“One of the most insidious actions of malware, is abusing the audio and video capabilities of an infected host to record an unknowing user. Macs, of course, are not immune; malware such as OSX/Eleanor, OSX/Crisis, OSX/Mokes, and others, all attempt to spy on OS X users. OverSight constantly monitors a system, alerting a user whenever the internal microphone is activated, or the built-in webcam is accessed. And yes, while the webcam’s LED will turn on whenever a session is initially started, new research has shown that malware can surreptitious piggyback into such existing sessions (FaceTime, Sykpe, Google Hangouts, etc.) and record both audio and video – without fear of detection.”
Sound good? If so, it’s a free download that is easy to install on a Mac with either macOS or Mac OS X:
If you’re interested in this app, simply download Oversight and run the installer (it can be just as easily uninstalled later if you decide you do not need it).
Once installed, Oversight is small and lightweight running quietly in the background, and it will alert you anytime the Mac microphone or webcam FaceTime camera are attempting to be activated. You can then directly intervene and either allow the webcam or microphone access (for legitimate use), or deny it (for theoretical illegitimate use).
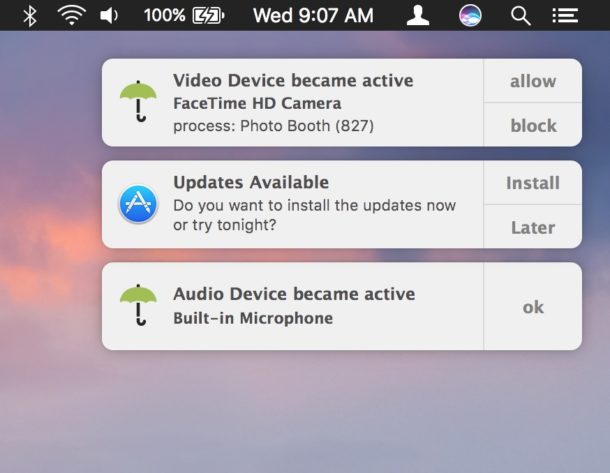
Keep in mind that Oversight does not differentiate between legitimate and illegitimate use of the webcam and microphone on your Mac, that is up to you. For example, you will get a notification alert that the microphone and FaceTime camera are trying to be accessed when you open an app like Skype, Photo Booth, FaceTime, or are recording a video on your Mac with the webcam, but since those applications legitimately use the computers microphone and camera they are probably nothing to be concerned about (assuming you have launched them yourself anyway). On the other hand, if out of the blue and with no provocation if you see a process has attempted to access your microphone, that could potentially be an unauthorized attempt to use the microphone and you could choose to reject it and block the device access with Oversight. Whenever possible, Oversight will attempt to notify you of the process name and PID, but sometimes you will see blank notifications of access anyway – again just think about what apps you are using and if they have any reason to use your camera or microphone, similar to how you can control this type of access in iOS for Photos, camera, and microphone.

This is a software solution which is quite a bit more fancy than the low-tech solution of putting tape on your web camera like the FBI Director does and many security professionals do. You could always use Oversight along with some tape too if you’re extra concerned about your Mac webcam or microphone access and want to be sure nothing fishy is going on from camfecting or otherwise.
While apps like Oversight could be considered overboard and unnecessary for many Mac users, others who are privacy conscious or in fields where higher security matters may find them to be helpful. I’ve personally noticed a particular web browser will occasionally attempt to access the microphone on my Mac from time to time without an obvious reason which I find to be… curious… and Oversight notified me each time. It’s not for everyone, but if you want to be notified when something is trying to use your Mac camera or microphone, check out the app yourself.
Do you have any thoughts or opinions on apps like Oversight? Let us know in the comments.


So, the green LED is hardwired to turn on, which will inform you anyway.
And as the developer admits, it won’t protect you against malware that hijacks legitimate use of the camera and audio.
So, what’s the point of this software (which itself requires root and might be a vulnerability in itself)?
the green light is not hardwired to turn on. That’s a false belief. Microphone only defaults to no light. Camera can be invoked in ways that avoid green light.
I painted over the lens and disconnected both the camera cable and the microphone cables from my motherboard. Why leave an unused door unlocked?
This might seem overly paranoid, but how do we know that Oversight itself isn’t a surveillance tool? Is it open source?
That would be a classic counterintelligence maneuver! Very fair question and it certainly makes you wonder because it’s not open source, so you never really know…. it asks for your admin password after all. Maybe it is key logging, capturing snapshots, mic pickup, camera, who knows? I don’t know how much Apple protects this stuff by default, but after you install something… anything goes.
If you had LittleSnitch activated as well you might be able to detect if outbound network traffic is occurring. I suspect it would be smart enough to disguise under a different PID because OverSight and OverSightHelper do not have any network activity…
Now I’m curious!! Could use lsof to try and detect process file access… the plot thickens! What if it’s the Ruskies?!
I wear a full facemask and don’t speak when I use my laptop.
Something similar in working is “Micro Snitch”: https://itunes.apple.com/us/app/micro-snitch/id972028355
Thanks, good tip! Used Littlesnitch for a while however the output list of events was almost overwhelming with what appeared to be Apple events.
I would add to the list by adding RansomWhere from the same developer.
Interesting, but would it not be quite feasable for the malware to also suppress the alert? That’s the beauty of a little piece of tape though that won’t stop the microphone. Little snitch is always good….
So what particular web browser likes to activate the microphone? Is there any (good) reason for protecting the makers of this browser from being exposed?
It was probably a webpage being overly aggressive with getUserMedia, but it happened on multiple occasions and I was never able to conclusively identify what was causing it. Nonetheless I switched to a different browser (currently using Safari Tech Preview) and it hasn’t happened since. Could have been a fluke, who knows? But weird, anyway.
I use Oversight and KnockKnock from the same developer and would recommend them both, great security tools. LittleSnitch is excellent too.
If I remember correctly the developer Patrick Wardle used to work for the NSA so he is quite sharp on this topic.