What is AKAuthorizationRemoteView and akd process on Mac?
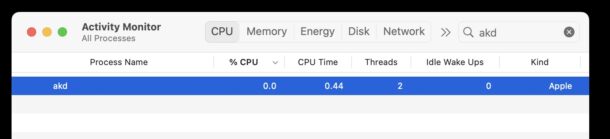
Some Mac users may discover a process called AKAuthorization, AKAuthorizationRemoteView, “AKAuthorizationRemoteViewService”, and/or akd, running on macOS. Sometimes these process may be taking up inordinate amounts of CPU, which can add to the confusion, or concern. And, it’s not unusual for Mac users to find the “AKAuthorization remote view” name to sound a little suspicious, which may raise concerns about spyware, virus, or being hacked.
So what is AKAuthorizationRemoteView, AKAuthorizationRemoteViewService, “AKAuthorization remote view”, AKAuthorization, and akd, and why are you seeing them running on your Mac? That’s what we’re here to discuss.
What is AKAuthorization and akd on MacOS?
It turns out that akd and AKAuthorization are part of Apple’s AuthKit framework, and is typically used to authenticate iCloud, Apple ID, and other Apple services.
Thus, you may see these processes running in the background on a Mac at any time, but particularly if something related to authenticating, iCloud, or an Apple ID is active (for example, any behavior with iCloud, like iCloud Photos downloading, or an iCloud backup running, or even Safari tabs being synced).
akd is the background service or authentication daemon itself, where as AKAuthorization and related processes including AKAuthorizationRemoteView (often with “Safari”, “Messages”, “Mail”, or similar apps included) are processes that run related to authentication services on the Mac, often with other apps or services.
Occasionally, if you discover that akd or AKAuthorizationRemoteView service are running with a lot of CPU usage, it’s often because there’s a temporary blip in logging in or authenticating, or, as I recently discovered, if you change an Apple ID password you may see these processes spin up and run too.
Was I hacked? Is AKAuthorization or akd spyware or a virus?
No. The related processes of akd, AKAuthorization, AKAuthorizationRemoteViewService, and other “AKAuthorization remote view” processes are not spyware or malware, or anything nefarious at all. These processes are from Apple and a normal part of macOS.
But, because of the “AKAuthorizationRemoteView” and particularly the “Remote View” part of the process name in particular, many users have suspicions about these processes, and you certainly are not alone for wondering (see here, here, here, and here to know that you’re in good company with reasonable concern about the name of these processes).
It’s good to be vigilant about what software is running on your Mac, but it’s helpful to remember that, for the most part, malware is not a common occurrence in macOS, and that Apple has multiple built-in security mechanisms with macOS to prevent malware, viruses, and junkware from impacting a Macintosh.
Where is akd and AKAuthorization located on the Mac?
If you’re the curious type, you may be interested in knowing where these files and frameworks are kept within the Mac operating system.
Components of the akd process and other AuthKit data are kept in the following locations on macOS:
/System/Library/PrivateFrameworks/AuthKit.framework/
The akd daemon itself is located at the following location in MacOS:
/System/Library/PrivateFrameworks/AuthKit.framework/Versions/A/Support/akd
None of these files should be modified, deleted, edited, or removed in any way. Doing so may cause macOS and many apps to not perform as expected, or even break completely. Never modify system files.
If you want to learn more about Authkit, from a developer perspective, you can read Apple’s documentation on Authentication Services here.
Do you have any extra insight into or experiences with AKAuthorizationRemoteView, akd, or other AKAuthorization processes on the Mac? Let us know in the comments!


It does seem to be another example of poor software engineering however, when an auth program requires upwards of 10% CPU on my M2 MacBook Pro. Seriously, why is it needing to devour so much CPU resources?