Encrypt & Decrypt Files from the Command Line with OpenSSL
Need to quickly encrypt a file from the command line? With OpenSSL, you can encrypt and decrypt files very easily.
For the purpose of this walkthrough, we’ll use des3 encryption, which in simple terms means a complex encryption algorithm is applied three times to each data block, making it difficult to crack through brute force methods. While we’re focusing on Mac OS X here, these commands will work anywhere that OpenSSL is installed, including older versions of OS X and Linux.
How to Encrypt Files with OpenSSL
The syntax of openssl is basic:
openssl [encryption type] -in [file to encrypt]
As mentioned before, we’ll use des3 for the encryption, and we’ll be using a text file as the input. We’re also going to specify a different output file to prevent any errors. Here is what the command would look like:
openssl des3 -in file.txt -out encrypted.txt
You will be asked to set and confirm a password before the encryption is complete, do not lose this password or you will lose access to the file.
Sidenote: You can also just use an input file with -in filename, but that may cause issues. To prevent any unexpected problems, do not specify the same file as the input and output. This means the original file will stick around either before or after encryption, and you will want to deal with that file individually, preferably through a secure delete method.
Decrypting Files with OpenSSL
openssl des3 -d -in encrypted.txt -out normal.txt
The previously set password will be required to decrypt the file.
Other than switching the placement of the input and output, where again the original file stays put, the main difference here is the -d flag which tells openssl to decrypt the file.
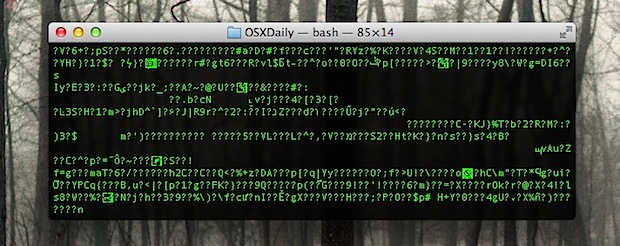
Naturally, you’re probably wondering what happens if you try to open an file that has been encrypted with OpenSSL without entering the password? You’ll probably get an error message, but if you force open the file with something like TextEdit, you’ll see the text “Salted” followed by a bunch of gibberish like so:
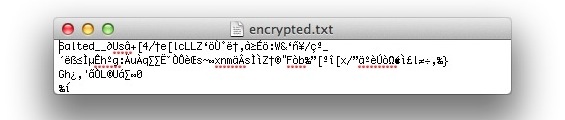
The file will remain unreadable until it has been decrypted through openssl again.
For more about file security, don’t miss some of our other posts, including password protecting a Mac, encrypting partitions, zip archives, files and folders in disk images, and even encrypting iOS backups to keep sensitive data from an iPhone and iPad secure.


I encrypted the file using OpenSSL under the same name and location, but now I am unable to open it! If I use the same code to encrypt the file but change the output name slightly, it was able to decrypt.
Is there a way around it? I encrypted a very important .dmg file!
How to encrypt and decrypt directories with openssl? Is this possible?
Yes, You would want to zip, tar, or gzip the directory first, and then encrypt and decrypt that archive.
[…] Get in the habit of using Secure Empty Trash anytime you are removing something that is truly sensitive and that you don’t want others to regain access to. Things like financial statements, credit card information, personal files and diaries, or deleting the source files and finished documents from openssl file encryption. […]
This is very useful information, I was curious to see if there is any way to actually encrypt the name of the file itself as well ?
Regards,
Deniz Rende
Thanks. It useful.
Neat. what about if you need to encrypt a fake file? The kind that you can “show package contents” on. These are technically folders aren’t they? This method fails on those files. Would we have to zip it first before encrypting?
Yeah, although that’s easy enough to do with a combination of:
zip -r file.zip package-file
openssl des3 -in file.zip -out encrypted.txt
Very handy! Thanks for the tip.
Niiiiice wwooorrk