Nmap for Mac OS X Explores Networks, Scans Ports, and More
Nmap is a powerful command line network discovery utility that lets you review network inventory, host response and uptime, and perform security auditing through port scans, OS and firewall detection, and more. Though it’s free (and open source) and ships along with many versions of linux, it doesn’t come standard with Mac OS X installations, and thus must be installed separately. Nmap is generally fairly advanced, but it has plenty of useful applications even for those of us who are not network administrators and security professionals, and it can also be helpful for simple network setup tasks and troubleshooting.
While installing nmap you will also have the option to install the full suite of network discovery utilities, including ncat, zenmap (requires X11), ndiff, and nping. These are all useful tools as well, so it’s a good idea to install them all along the way.
How to Install Nmap for Mac OS X
Using the DMG installer is the easiest way, but you can also build nmap yourself from source or get it through something like Homebrew or MacPorts.
To download the the dmg installer for nmap via nmap.org:
- Get nmap for Mac OS X (free)
- Install through the dmg, be sure to right-click and choose “Open” to get around the Gatekeeper warning if it’s still enabled
- Install the full nmap suite, or selectively choose whether to install ncat, ndiff, nping, etc
For installing Nmap on Mac with Homebrew, just run the following command:
brew install nmap
There’s no need to reboot, but you will want to refresh or open a new Terminal to have nmap found in your path.
Sample Usages of Nmap
Nmap works with both LAN and WAN IP’s and has near infinite applications, but we’ll cover a few commonly used simple tricks. Do note that its not unusual for very little information to be reported back from Mac OS X machines, particularly if the software firewall has been enabled and no sharing services are enabled. On the other hand, scanning a Windows PC or a network of Windows machines will often give you a huge amount of information and reveal many services, even if the Windows firewall is enabled.
Find Open Ports on Localhost
Nmap makes it very easy to find out which ports are open on localhost (that is, your computer):
nmap localhost
You might see something like the following reported back:
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
445/tcp open microsoft-ds
548/tcp open afp
6817/tcp open unknown
This let’s you know that SSH/SFTP, HTTP, Samba, and the Apple File Sharing protocol are all open on the localhost Mac, and shows which ports they’re running under.
For a Mac, toggling various options directly in the System Preference “Sharing” panel will directly impact what you see as running, whether it’s to activate the SSH and SFTP server and enabling remote login, turning on and off file sharing for Macs or Windows or both, screen sharing, or whatever else. Separately, if you started a local web server at some point (even the super quick python http server), you’ll also find those running.
Scan & List a Range of Local Network IP’s
You can also find information about other machines on your local network. We’ll assume your LAN has an IP range of 192.168.0.1 to 192.168.0.25, change those numbers as appropriate:
nmap -sP 192.168.0.1-25
If you don’t know the range, you can also use wildcards:
nmap 192.168.0.*
Scan & Detect Operating Systems
Using the same IP range concept as above, you can attempt to discover which operating systems and their accompanying versions are running on the networked machines. This does not always work, but there’s no harm in trying:
nmap -O 192.168.0.1-5
If nothing is reported back (not uncommon), you can try to use the –osscan-guess flag instead to try and guess which OS is running based on the services detected:
nmap --osscan-guess 192.168.0.2
Using Nmap with Alternate DNS Servers & Trace Route
Nmap is also really useful for troubleshooting internet connections, WAN issues, and publicly available assets, and it can be helpful when trying to figure out if a network issue is your network, an ISP, or somewhere else along the way. By using the –traceroute and –dns-servers flags you’ll be able to help determine what’s going on and where, and the latter is particularly helpful if you are having trouble accessing certain remote IP’s but are unsure if the host is actually unavailable or if your DNS servers are the issue.
The –dns-servers flag overrides system DNS settings for that scan. Here we’ll use nmap to scan through alternate DNS (Google’s DNS servers used in example) of yahoo.com:
nmap --dns-servers 8.8.8.8 yahoo.com
In this example, if yahoo.com is live through the alternate DNS but not available to you without specifying –dns-servers, you may have an issue with whichever DNS servers you are using rather than the host itself.
The –traceroute flag incorporates the familiar trace route ability in the scan, note this has to be run as root through sudo:
sudo nmap --traceroute yahoo.com
More Resources
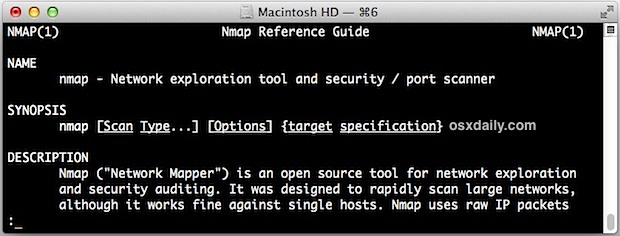
Nmap has much more to offer than what we mention above, you can see the full list of possible commands and flags by typing:
nmap --help
Or by summoning the manual page:
man nmap
If you’re interested in learning more, the nmap website is also full of great resources and offers extensive documentation.


The namp can work fine on terminal, while Zenmap GUI cannot be open with the words “LSOpenURLsWithRole() failed with error -10810 for the file /Applications/Zenmap.app”.
There is more to it. The package installer installs some update checker files, Zenmap, and other files. How about removing those?
I can’t run nmap in Terminal even after rebooting. I am running 10.8.3. What am I doing wrong?
For future reference, to re-initialize the shell’s path to be able to run newly installed binaries without logging out or launching a new terminal, “hash -r” in bash, and “rehash” in the c-shells.
Great simple trick, thanks!
How do I remove what the package installer did? Specifically nmap?
sudo rm -i `which nmap`
note the ` characters are backquotes; usually the same key as ~ but without pressing .
shift.
Thank you.