How to Secure Erase a Mac SSD / Hard Disk from Recovery Mode
![]() The newest Macs ship with a Recovery partition rather than a separate external reinstall disk, and if you’ve ever rebooted a newer Mac, iMac, MacBook Air, or MacBook Pro with an SSD from the Recovery partition to reformat the drive, you may have noticed that by default the “Security Options” button is greyed out in the Disk Utility options, seemingly preventing a standard “secure” erase procedure. The precise reason for this isn’t entirely clear, though some speculate it’s because writing 1’s and 0’s to an SSD can lead to performance degradation and a reduction in the drives lifespan, and that it persists even in the most recent versions of OS X suggests it’s not just a bug. Nonetheless, many users want the option for secure removal of data from the SSD. The most obvious solution to this problem is to boot the Mac from an external boot drive (here’s how to make one for Mountain Lion), but that isn’t always an option for everyone, but fortunately there is a workaround that lets you perform a secure erase directly from the Recovery partition itself.
The newest Macs ship with a Recovery partition rather than a separate external reinstall disk, and if you’ve ever rebooted a newer Mac, iMac, MacBook Air, or MacBook Pro with an SSD from the Recovery partition to reformat the drive, you may have noticed that by default the “Security Options” button is greyed out in the Disk Utility options, seemingly preventing a standard “secure” erase procedure. The precise reason for this isn’t entirely clear, though some speculate it’s because writing 1’s and 0’s to an SSD can lead to performance degradation and a reduction in the drives lifespan, and that it persists even in the most recent versions of OS X suggests it’s not just a bug. Nonetheless, many users want the option for secure removal of data from the SSD. The most obvious solution to this problem is to boot the Mac from an external boot drive (here’s how to make one for Mountain Lion), but that isn’t always an option for everyone, but fortunately there is a workaround that lets you perform a secure erase directly from the Recovery partition itself.
This is very much a workaround, as you’ll technically be erasing the drive twice in the process. The first time will not be the secure erase, it’s the second time formatting that will allow you to achieve the desired outcome. For users with an SSD drive, it’s important to note that using the secure formatting options like 7 pass and 35 pass could potentially lead to a reduction in drive life span, or performance degradation, though TRIM is thought to mitigate that risk. Be sure you understand that and are comfortable with that potential before proceeding.
Secure Format an SSD (or the OS X Boot Disk) via Recovery Mode
Though it may be obvious, it’s important to point out and to remember that this process removes all data from the drive, which then becomes unrecoverable due to the highly secure formatting options. Always back up important data before formatting a drive, or else it will be gone forever.
- Reboot the MacBook and hold down the OPTION key, then select the Recovery partition
- At the OS X Utilities menu, choose “Disk Utility”
- Select the hard drives primary partition (usually called Macintosh HD) from the left, then choose the “Erase” tab
- Under “Format” choose “Mac OS Extended (Journaled, Encrypted) – the “Encrypted” part is crucial
- Choose “Erase” and set a password for the encrypted partition, for now choose a simple password that’s easy to remember, then choose “Erase”
- Let the drive erase and turn into an encrypted format, this process can take a while depending on the drive type, size, and speed
- Now select the partition in Disk Utility again, and from the “Erase” tab choose “Mac OS Extended (Journaled)”
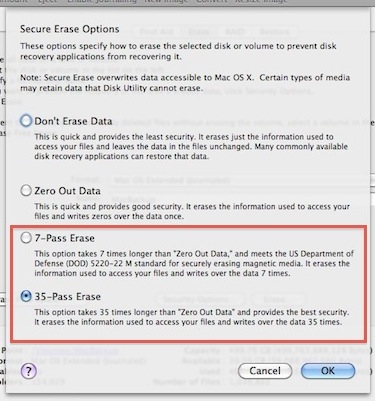
- Notice the “Erase Free Space” and “Security Options” buttons are now clickable as expected, choose “Security Options” and select your level of secure erasure, “35-Pass Erase” is by far the most secure but takes 35 times longer because it literally writes over the drives existing data 35 times
- Choose “OK” and let the secure erase proceed, when finished you will have a blank primary partition that has been securely formatted
The Macs hard drive has now been securely erased, entirely from the built-in Recovery partition, and without the need of an external boot drive or disk. At this point you may want to repair the disk since you’re already booted into Recovery, or you can exit out of Disk Utility and re-install a clean version of OS X on the Mac if desired, or do whatever else you want with your newly blank hard drive space.
Note, this does not remove the Recovery partition. You can do that separately if desired, but it is not recommended as you will be unable to restore OS X or boot into Recovery mode once it has been removed, thereby requiring the usage of an external boot disk to install Mac OS X back onto the machine.
Heads up to David for passing along the basis of this trick from MacRumors Forums. We have confirmed this works on a MacBook Air with a solid state drive, but if anyone knows of a better method of secure formatting the SSD drives of Macs or the boot disk by way of Recovery Mode, let us know in the comments!


Doesn’t work for me … going round and round with erase extended/journaled/encrypted and then erase extended/journaled – but never any options for secure erase…
The Secure Erase has been removed from the GUI Disk Utility. It is still available in the command line diskutil. However SSD’s should not be multi-pass wiped it is harmful to the medium. Multi-pass wipe is only for magnetic old spinning rust drives. You should turn on FileVault2 and encrypt the SSD. Then just erase it when it is done and reinstall macOS. That will make it pretty much impossible to recover.
For secureErase open Terminal and type diskutil secureErase and hit Return. It will show the options which are the same as described here. 35 pass is ridiculous if its a traditional HDD that you can replace you might as well pull the drive out and drill 4-5 holes through it and install a new HDD or better yet an SSD. Faster than and cheaper on time then letting a 35 pass wipe run.
My problem is reverse. First 11″ MB Air to apple for diagnosis. 20 mins explaining I could not let them erase anything before I backed it up yet they assured me all will be be fine just diagnosis and call me. Week later they called- it was sent out of store to headquarters and completely erased with new operating system installed. Is everything really gone (3 books I was writing, photos of recent nurdered family member, medical records, Photoshop, etc). I have it in writing they were not to do anything w/o my consent. Employee made mistake, Apple paid for DriveSavers to try recovery but SSDs are not their thing. Zero recovery thus far. Apple nor DriveSavers will divulge what they did.
Yes unfortunately the way an SSD volume works it makes it very difficult to recover deleted data from them if there is not immediate action taken (as in within minutes), this is because SSD volumes use a service called TRIM which ‘cleans up’ the drive. Once an SSD has been formatted it is notoriously difficult to recover data from, DriveSavers may be right, but you can try to find a SSD specific drive recovery service, I would temper expectations however because it is often impossible to recover the files. If the drive was ‘secure erased’ as described in this article, it would be entirely impossible to recover the files.
Sorry to hear about your situation. I know it’s not much consolation for lost files and data, but in the future be sure to backup the Mac to an external hard drive on a regular basis, Time Machine makes it easy. Also, Apple routinely formats any Mac or iOS device sent their way for simple unrelated repairs, I am not sure why they do this aside from troubleshooting obvious software issues, but it has happened to me and relatives as well (got a keyboard replaced, Mac was formatted).
The lesson is really about backups, backup your data always. And assume if the computer goes in for service, it will be formatted.
“35-Pass Erase is by far the most secure” is not accurate for SSDs or physical disks. The paper this was based on was theoretical and data retrieval was never proven with even a single pass on magnetic disks. It has even less relevance for SSDs.
The DOD 7 pass standard was also based on magnetic disks, and since 2007 the DOD does not recommend overwriting with any number of passes–only physical destruction of the disk.
tl;dr – Do a single pass unless you’re Snowden. If you are Snowden, burn your disks with a blowtorch.
35 cycles method “provides best security”. Shouldn’t 36 cycles be better? :o
Umm… 7 overwrite cycles – varying from 0s, 1s, to random is pretty damn good for a regular drive (HDD).
Melting the drive with thermite or something else is probably the most reliable way of preventing the data from being recovered. :)
Hammers and very big magnets can also work well. Hammers – the ultimate tool!
Big surprise. MAGNETS DO NOTHING TO SSDs. Why? Because they are not magnetic drives. Same reason you can put your mobile into a degausser, non magnetic HDD’s are not effected by magnets.
The hammer will work to a degree, but only if you manage to break the data storage chips.
7 overwrites is excessive, and generally a complete waste of time on an SSD.
According to the NIST Special Publication 800-88 Rev1, Page 38
– The Clear procedure should consist of at least one pass of writes with a fixed data value, such as all zeroes.
– Two options are available for Purge.
1. NVMe Express format if supported.
2. Cryptographic Erase through TCG Opal SSC or Enterprise SSC by issuing commands as necessary to cause all MEKs to be changed. Optionally followed by User Data Erase or Clear procedure.
For SSDs especially, I’d recommend using Parted Magic’s ATA secure erase app. Unlike the methods mentioned above, the secure erase triggers the drive’s native method for wiping the drive – no zeroing or potentially leaving old data in spare blocks on an SSD. I’ve used this on multiple MacBook Pros and MacBook Airs’ OEM drives without issue. It usually takes less than two minutes to complete as well.
The only way you should secure erase SSD is using ATA Secure Erase. Which is pain on Mac’s. OCZ is only company who offers a bootable USB image with script that runs ATA Secure Erase commands on Mac’s. Any bootable linux image like ubuntu, mint, & etc has “hdparm”, which will allow you to run ATA Secure Erase commands. See link below for more info on ATA Secure Erase.
https://ata.wiki.kernel.org/index.php/ATA_Secure_Erase
FYI – ATA is the only technique that purges all the data stored on a hard disk drive using internal commands. When using this method on SSD, it sends small electric current to reset Nand. Also known as “electronic data shredding.”
There is a reason this option isn’t there. There is no way to guarantee removal of data on a SSD. The SSD keeps spare blocks for wear leveling and garbage collection. Those don’t get overwritten reliably.
If you have sensitive data, encrypt your drive before putting the data on it.
Interesting workaround and it’s valuable, but for SSD owners unless you have *VERY* sensitive data on the SSD and you plan on transferring ownership, I would not recommend doing this since it creates a lot of unnecessary writing to the disk, which is damaging to how solid state drives work.
Keep in mind that data evaporation happens quickly on an SSD because of TRIM. In laymens terms that means you could just format the drive and reinstall OS X as usual, and throughout the standard process of using the freshly formatted Mac, all data that used to exist on the drive will vanish.
Here’s a great article about this, where it demonstrates that data disappears after anywhere from 10 minutes to 1 hour, depending on usage of the drive
http://samsclass.info/121/proj/ssd-evaporation.htm
Just my 2 cents
BTW none of this is applicable to a traditional hard drive, so format 3500 times all you want.
Unlike physical disks, there is little to no chance of “ghosting” of data on an SSD. Once deleted from the block, it’s gone. One overwrite or one TRIM hit is enough to make it gone. The only worry one might have is that a block might not get TRIMmed off.
IMHO, there is only three classes of trust for an SSD holding data:
1. Quick format, and the TRIM will wipe the data you left in an hour or so. This is plenty for most of us.
2. Overwrite the entire disk once with zeros. If the drive is smart enough, it’ll translate this to a TRIM wipe, and if it isn’t, you’ve only lost 1 cycle per cell.
3. Thermite the drive.
2 is good enough for anyone this side of Top Secret, and if you’re that deep in security you aren’t giving a drive away anyway.