Safari 8.0.6, Safari 7.1.6, & Safari 6.2.6 Released for Mac Users
![]() Apple has released a series of security updates for the Safari web browser, versioned as 8.0.6 for OS X Yosemite, Safari 7.16 for OS X Mavericks, and Safari 6.2.6 for OS X Mountain Lion.
Apple has released a series of security updates for the Safari web browser, versioned as 8.0.6 for OS X Yosemite, Safari 7.16 for OS X Mavericks, and Safari 6.2.6 for OS X Mountain Lion.
Release notes accompanying the small update mention that it “contains improvements to security”, making it recommended for all Mac Safari users to download
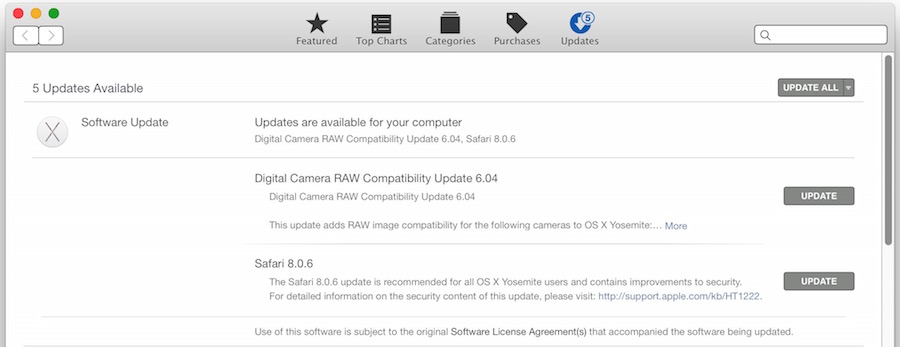
Mac users can find the update available now through the Mac App Store by going to the Apple menu and visiting the App Store Updates section. The update is quite small and does not require a reboot, though users will need to quit out of Safari to install the update.
Complete security notes with specifics about what has been addressed in the Safari update, courtesy of Apple Support, are repeated below:
Safari 8.0.6, Safari 7.1.6, and Safari 6.2.6
• WebKit Available for: OS X Mountain Lion v10.8.5, OS X Mavericks v10.9.5, and OS X Yosemite v10.10.3 Impact: Visiting a maliciously crafted website may lead to an unexpected application termination or arbitrary code execution Description: Multiple memory corruption issues existed in WebKit. These issues were addressed through improved memory handling. CVE-ID CVE-2015-1152 : Apple CVE-2015-1153 : Apple CVE-2015-1154 : Apple
• WebKit History Available for: OS X Mountain Lion v10.8.5, OS X Mavericks v10.9.5, and OS X Yosemite v10.10.3 Impact: Visiting a maliciously crafted website may compromise user information on the filesystem Description: A state management issue existed in Safari that allowed unprivileged origins to access contents on the filesystem. This issue was addressed through improved state management. CVE-ID CVE-2015-1155 : Joe Vennix of Rapid7 Inc. working with HP’s Zero Day Initiative
• WebKit Page Loading Available for: OS X Mountain Lion v10.8.5, OS X Mavericks v10.9.5, and OS X Yosemite v10.10.3 Impact: Visiting a malicious website by clicking a link may lead to user interface spoofing Description: An issue existed in the handling of the rel attribute in anchor elements. Target objects could get unauthorized access to link objects. This issue was addressed through improved link type adherence. CVE-ID CVE-2015-1156 : Zachary Durber of Moodle


The bookmarks system on Safari 6.2.6 sucks. The bookmarks bar and menu only open as a side bar and are harder to read and require more steps to open and close them. Not only that the browser pinwheels and crashes on many sites.
Programmers love to change things without improving a damn thing and often make things worse. This is especially true of Apple software.
Re this or thats better its a tool if you are most people you buy your tool at home depot if you are a cabinet maker you uses special tools. me id \f it give me my news and simple stuff thats all i need how bizzy could i be if my safari is so fast i am not saving lives with it
I’ve noticed a definite improvement, but, not complete (8.0.6/Yo). Part of the issue is probably Flash, which I wish was totally dead. If Hulu would let us watch free with Hulu app on ATV or iOS, I would be able to get rid of Flash on my Mac (you have to pay for Hulu+ for ATV/iOS…which I refuse to do, as you still get commercials/ads). As far as I know, there are no sites I use that depend on Flash, but, I may come across issues when I get rid of flash.
Yes, I could use Google Chrome, but, I just did a test, and it still uses twice as much processing power for same flash video played with Safari, as it uses emulation. So back in the Trash can for Chrome.
I noticed immediate problems with Safari’s update on both Yosemite & Mountain Lion…
Really, really, really wish Apple would STOP with these gimmicky new features and get back to building the MOST reliable OS in the world ( Yosemite has me to the point of considering Windows 10 for professional graphics work, when it’s officially released ).
What problems are you noticing on this update with Mountain Lion?
Side note: If you’re running 10.10.4, the update doesn’t show up at all.
Thank you! I’ve been wondering why the update is not there.
I don’t know why people use Safari. Lynx is so much better and faster!
You can run Lynx in OS X if you want to
https://osxdaily.com/2011/07/26/get-lynx-for-mac-os-x-10-7-lion/
Because for 99% of us, it works fine. It syncs open tabs, bookmarks, reading lists, and other key items across all of your personal Macs. Additionally, it’s built into the core of the OS, uses the least amount of system memory, isn’t prone to constant crashes.
Don’t be so narrow-minded. Just because YOU don’t care for something doesn’t mean it’s the same for everyone else.
And just because it works for you, do not assume it works for the other 99%. FAILed logic.
Well, it works for me, too. So . . . 98%.
Safari is still the fastest browser on the Mac that works with current codecs. I have not used Lynx, but, I looked at the link, looks very old school.