How to Check for Compromised or Leaked Passwords on iPhone & iPad with Security Recommendations

Have you ever wondered if the passwords to any of your online accounts have been compromised in a data breach? You’re certainly not the only one in that regard, but now you can now check for breached password security easily right from your iPhone and iPad.
In the latest versions of iOS and iPadOS (14 and later), Apple has added a security feature called “Security Recommendations” that would provide security alerts for the passwords stored on iCloud Keychain. If one or more of your accounts use a password that’s easy to guess, uses a sequence like 123, or a password that was previously leaked on the web due to a data breach, you will be alerted and prompted to change the password for those accounts.
Do you want to make sure that none of the passwords you use pose a security risk? This article will cover how to check password security recommendations on both your iPhone and iPad.
How to Check Password Security Recommendations on iPhone & iPad
Since this is a feature that was introduced alongside modern versions of iOS and iPadOS, make sure that your device is running iOS 14/iPadOS 14 or later before going ahead with the procedure. Assuming you’re on a modern system software version, here’s all you need to do next:
- On iOS 26 and newer, open the “Passwords” app directly. On earlier versions of iOS, head over to “Settings” from the home screen of your iPhone or iPad.

- In the settings menu, scroll down and tap on “Passwords”.

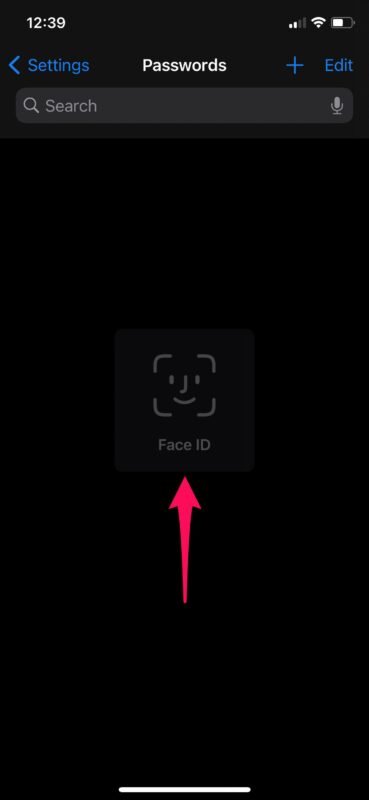
- Next, you will be asked to authenticate with Face ID or Touch ID depending on your device before you’re allowed to view the iCloud Keychain data.

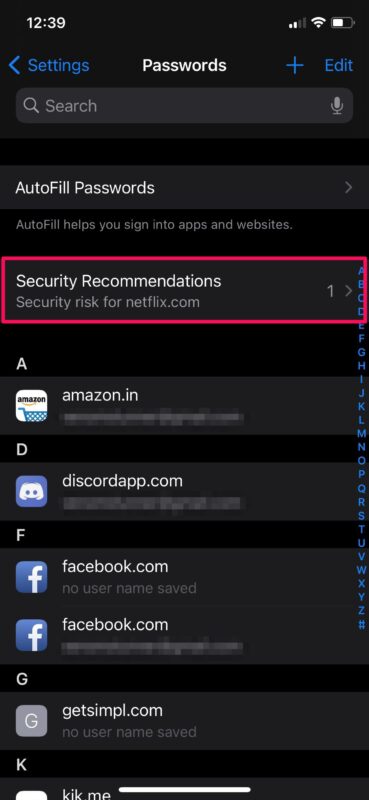
- Here, tap on “Security Recommendations” located right above the list of passwords.

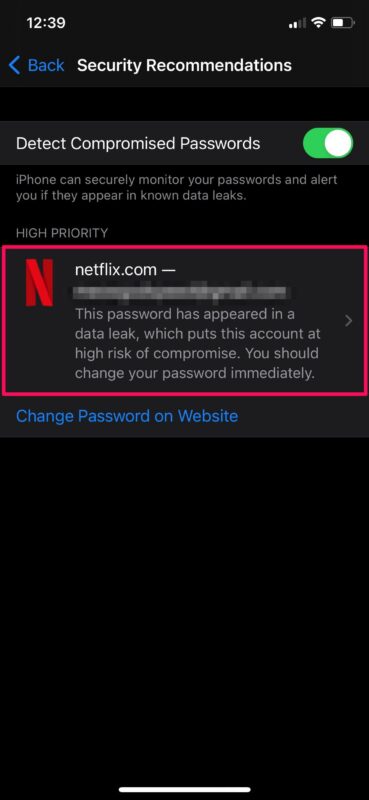
- If any of your accounts are using a password that’s weak, easy to guess, or appeared in a data leak, it will be displayed here. Tap on the account to view more details.

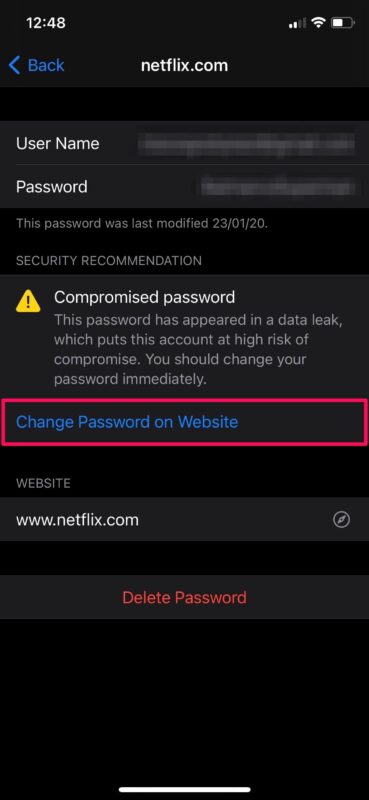
- You’ll be prompted to change the compromised password. Tap on “Change Password on Website” to continue with this.

When browsing through the list, you may see a notice saying something like “This password has appeared in a data breach, which puts this account at high risk of compromise.” and if you do, that’s a good indicator to change passwords associated with that account or reused elsewhere.
Assuming you followed along, you’ve now learned how to check for Security Recommendations related to your online accounts stored on iCloud Keychain. That was pretty easy, right?
Thanks to this feature, you can easily make sure that none of the passwords that you use are weak, or compromised in a data breach. This helps to minimize the security risks associated with having online accounts, particularly if you share passwords between services (which is generally not recommended by security experts, but many users do it anyway out of convenience).
If you’re wondering how this feature works and the privacy implications of it, according to Apple; “Safari uses strong cryptographic techniques to regularly check derivations of your passwords against a list of breached passwords in a secure and private way that doesn’t reveal your password information — even to Apple.”
Don’t forget you can also manually add passwords and logins to Keychain on iPhone and iPad too if you want them to be checked by this feature.
In addition to this, Apple has made some huge improvements to privacy with modern iOS and iPadOS releases. Thanks to features like Approximate Location, Limited Photos Access, Privacy Report, and recording indicators, users now have complete control over what data third-party apps and developers are able to access from their iPhones and iPads. Check out more privacy specific tips and tricks here if the subject interests you.
We hope you were able to use Security Recommendations to check and update weak or leaked passwords. What’s your take on Apple’s game-changing privacy features? Have you been enjoying the other new additions to iOS 14 so far? Do share your valuable opinions and experiences in the comments section down below.



After enduring the worst cyber warfare and identity theft, now confirmed by the Magistrates Court, I’ve come across something that could cripple us through a cyber attack.
Apple devices are being compromised through the Log4Shell exploit. This exploit allows total control through the back end and uses whats known as zero click installation of spyware. This spyware is not installed by clicking on a malicious link, or answering a malicious call. When someone calls you, even not answering that number will allow the malicious connection.
This exploit was listed as critical by the Australian Government in December 2021, but they don’t understand how critical this is.
Apple apps like Messages, Stocks, Translate, and other apps that the user can’t remove, are being used to access peoples devices through Log4Shell exploits.
Why is this so terrible? Once access is gained, your device is constantly broadcasting a Bluetooth and wifi connections that can’t be turned off. It also can’t be seen as the controls are deep within the Accessibility menu, not in the main Bluetooth and wifi setting menus.
Somehow, this spyware and exploit installs a virus on your home wifi. From there, anything that it is connected to (including all smart home products) are infected. I’ve found this virus in phones, modems, smart tv’s, even car stereos. While we watch the physical pandemic taking place, under our noses is the real threat – a cyber pandemic, where this e-virus infects anything we connect to, and connects outbound to spread it to others. I never turn on my Mobile Hotspot EVER. Yeah I have a growing list of hotspot connections with data transferred.
Without you knowing, all your travels, allow anyone around you to connect to you, and download your personal info from your device within seconds – phone serial number, financial details and mobile carrier details (imei, sim info,) everything.
Remember the old credit card skimmers? It’s like that, only the person walking or more so, driving past you that looks innocent, is in fact harvesting every detail about your life in a brief passing. Intently. Your identity gone. In a drive by. Just like what happened to me.
Where the fun starts is that this issue allows your phone to be mirrored 24/7. Everything done of your screen recorded. Camera and microphone on all the time.
So how can this be found?
I download legit apps through the App Store then when opened the screen jumps, and in a micro second, the web page appadjust.com disappears, then I’m left with what looks like a kindergarten kid developed the app. I was wondering why my Trend Micro app wouldn’t work, and how my home security app could have the logs deleted remotely, and that’s because the app that I’m left with isn’t secure, but looks like it is. Check the app version number vs that listed on Google as the most recent and the numbers are very different. Read the app license information and the app has no connection to the actual company’s app that you wanted to download.
There is a Chinese and Japanese Keyboard in my iCloud backup settings that I can’t find or delete elsewhere. I only speak English and wonder why an English keyboard isn’t listed. The only keyboard I use. No one at Apple can explain why it’s there. Apparently everyone has it set like that, but if it can’t be explained, there’s bigger issues. Here’s just one access point.
The calls I’m waiting to receive are silenced so I can’t hear them, nor do they show in my notifications… they show as a missed cal in my logs and nowhere else.
This is absolute cyber warfare, and an electronic takeover. Only it’s not just happening to me, there’s others I know in the same boat.
This is very new, very advanced, and has the ability to cripple anything we connect to, in such a devious and hidden way that can only be uncovered by second guessing the settings we barely use. They’re targeted because we never use them, and don’t understand them, so we ignore them. The Accessibility menu in iPhone iOS holds the key to how these criminals can use our devices to spread this crippling virus that doesn’t go away no matter how many factory resets.
This shows that our highest level of cyber security is not enough now. A factory reset now doesn’t remove this virus, and we are spreading this virus to everything we connect to. Think about that. An electronic virus that is now the same as a physical virus, it spreads itself. Advanced huh ?
I have dozens of screenshots to show evidence of everything I’ve listed happening, along with screenshots of all my attempts to notify the AFP of this activity blocked.
Great post. Unfortunately the the Apple tool has a very aggravating problem. The “Update password on website” tool does not update the password in the keychain. If you haven’t copied down the long “strong” password you are totally hosed the next time you try to log in from your device! I had to type in the long password that I had fortunately written down and only then did I get a prompt to update my keychain.
Another service that does a similar function is https://haveibeenpwned.com/.