OS X 10.9.2 Update: Fix for Mail Problems, SSL Security Flaw, & More
Apple has released OS X 10.9.2, a fairly major update to OS X Mavericks that includes resolutions to many problems and bugs encountered by Mac users. Critically, the OS X 10.9.2 update patches the SSL / TSL vulnerability for Macs that was fixed earlier for mobile devices with the iOS 7.0.6 update. The SSL fix alone makes the 10.9.2 update a particularly important release that all Mac users running Mavericks should install as soon as possible.
The OS X Update 10.9.2 also resolves remaining issues with OS X Mail, including resolutions to new email retrieval from services like Gmail and Outlook, fixes the Mail Archive problems, and the bundled SMB fixes should solve some of the issues encountered within the Finder. Separately, some additional features have been added to OS X, including native FaceTime Audio support, FaceTime call waiting support, iMessage blocking, and a variety of other stability and performance improvements.
Download OS X 10.9.2
The simplest way for most users to download and update to OS X 10.9.2 is through the Mac App Store, accessible through the Apple menu by choosing “Software Update”. The download will be found within the “Updates” tab of the application.
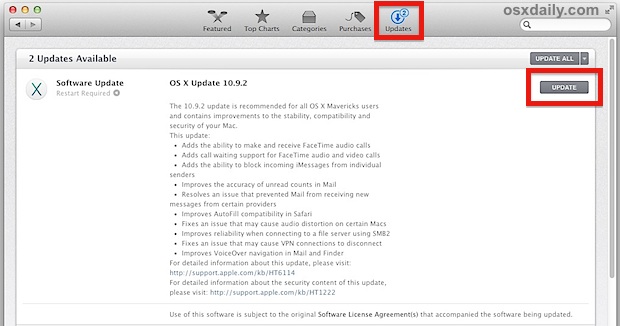
Downloaded through the App Store, the OS X 10.9.2 update weighs in between 460MB and 800MB, depending on the Mac being installed on. The final build for OS X 10.9.2 is 13C64.
As always, start a Time Machine backup and let it complete before installing any system updates, it is unlikely something will go wrong but it’s always better to be safe than sorry.
Users who have multiple Macs that need updating may wish to install OS X 10.9.2 through a Combo Updater, which can be directly downloaded here from Apple or through thegeneral Support Downloads website.
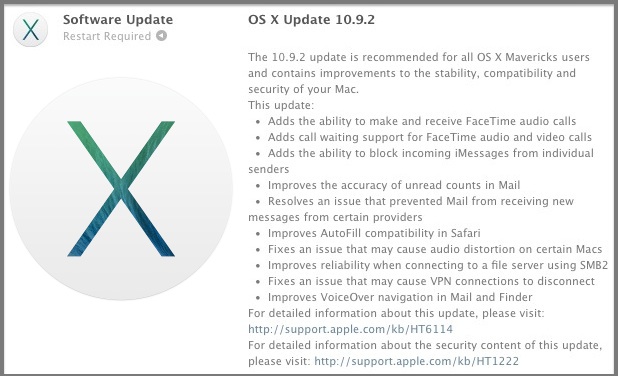
OS X 10.9.2 Release Notes
The release notes bundled with the Mavericks 10.9.2 update are as follows. Notably, there is no specific mention of the SSL / TSL security bug or a fix for it for Macs, but we can confirm the SSL bug has been patched with the 10.9.2 final build.
- Adds the ability to make and receive FaceTime Audio calls from OS X to OS X and to iOS
- Adds call waiting support for FaceTime audio and video calls
- Adds the ability to block incoming iMessages from individual senders
- Includes general improvements to the stability and compatibility of Mail
- Improves the accuracy of unread counts in Mail
- Resolves an issue that prevented Mail from receiving new messages from certain providers
- Improves AutoFill compatibility in Safari
- Fixes an issue that may cause audio distortion on certain Macs
- Improves reliability when connecting to a file server using SMB2
- Fixes an issue that may cause VPN connections to disconnect
- Improves VoiceOver navigation in Mail and Finder
- Improves VoiceOver reliability when navigating websites
- Improves compatibility with Gmail Archive mailboxes
- Includes improvements to Gmail labels
- Improves Safari browsing and Software Update installation when using an authenticated web proxy
- Adds additional layers of awesomeness to OSXDaily.com readers who read release notes
- Fixes an issue that could cause the Mac App Store to offer updates for apps that are already up to date
- Improves the reliability of diskless NetBoot service in OS X Server
- Fixes braille driver support for specific HandyTech displays
- Resolves an issue when using Safe Boot with some systems
- Improves ExpressCard compatibility for some MacBook Pro 2010 models
- Resolves an issue which prevented printing to printers shared by Windows XP
- Resolves an issue with Keychain that could cause repeated prompts to unlock the Local Items keychain
- Fixes an issue that could prevent certain preference panes from opening in System Preferences
- Fixes an issue that may prevent migration from completing while in Setup Assistant
The complete security specific notes can be found here.
Additional Security Updates for OS X Mountain Lion & Lion Available Separately
Aside from the OS X Mavericks 10.9.2 update, there is a Security Update to OS X Mountain Lion and OS X Lion Security Update available for users who are continuing to run Macs with older versions of OS X. Those updates can also be found in the Mac App Store on those machines, or downloaded directly from Apple as available here Security Update 2014-001 (Mountain Lion) and Security Update 2014-001 (Lion).
As usual, it is generally recommended to install the latest version of OS X available to you.


I’m getting angry and frustrated with Apple. OS X above 10.7.5 not worth the move. Still pissed off about removal of Java and the total destruction of Airport Utility. Why not try plug n play? UPnP. Oh no we gotta complicate it! Grrrrr..
I left All micro junk 15 yrs ago for plug n play Apple. NAT- Pmp sucks without the port mapping interface for opening ports that should open themselves. U know the one the update destroyed along with hot coffee. Oh then there’s the losing of 5000.00 plus of purchased iTunes media. Oh but we can’t merge your Apple ID or have a process available for email companies that fail. Don’t mind premium prices. Hate being robbed! Come back Steve!!!
I can’t seem to be able to get the jailbreak working for the macs now.
is possible to do i wonder?
Ha ha, that’s one of the reasons they want you to upgrade!
Thought the SMB2 might be more *reliable*, it’s still shockingly *S*L*O*O*O*W*W* as in 2-3MB/sec copying via Finder vs 50+MB/sec inside a VMWare Win7 VM inside the same laptop ;(
Q: I realize, after the update, one can go to Apple Menu>About this Mac and see the version, but is there any other way to determine that the update was installed successfully?
-Thanks.
Gawd, why would would you want another way of doing this?
After the update can no longer send emails anymore from my gmail / business account. Really really annoying.
Why can’t the two gorillas on the block find a way to work together to make life for users easier.
And obviously it is impossible to get through to a customer rep from either of the two companies.
It got rid of the annoying iPhoto warning about screen resolution, when running at 720p.
Mail is NOT fixed and it is NOT limited to GMAIL. It is limited to IMAP and the same problems still exist. Have to take all accounts offline and back on to start receiving mail again. Happens multiple times during the day. Just on IMAP accounts and I don’t use any Gmail.
Might kill your internal and external cams. Like it did to me.
https://discussions.apple.com/thread/5939338?start=15&tstart=0
Mail is partially fixed, but not entirely. Mail inbox is still not in sync with gmail version (which is real).
“The OS X Update 10.9.2 also resolves remaining issues with OS X Mail”
Not according to reviews on MacUpdate. More than a few are reporting the damn application continuously hangs and crashes.
Will wait longer.
Not showing as available on mine (10.9.1). Possibly as I’m in the UK?
Boring…! It’s not gonna change the facts that Mavericks still sucks…!
Snow Leopard FTW…!!!
Was the sleep/wake issue fixed in 10.9.2? I have a Macbook Pro, with this issue, even though I have read it was just Macbook Air?
Coming out of sleep, I end up with display corruption and then an automatic reboot.
Thanks
Now my Mac will not connect to inet. It shows wireless is connected but nothing.
All is well now, had to restart modem, duh? Lol.
Software Update showed nothing for Snow Leopard.
Snow Leopard (10.6.5) is probably not effected by the SSL bug
gotofail. showed my Snow Leopard to be good! Thanks…
Snow Leopard didn’t get an update because the system works well as an Apple system ever did or ever will. Apple will make you change somehow, someday. Legacy support is for suckers.
Snow Leopard does what I need it to do on my mid 2007 macbook.
FIX THE LABELS! Make the Finder able to use the label system in Mountain Lion and prior OSs.
Sheesh.
Yes.
Instead of a yellow line or a blue folder icon, we have to look for yellow dots and blue dots. Poor design.
Safari runs better.
With Mavericks on my Spring 2009 Macbook, Safari would hang up and give me the beach ball frequently when I scrolled down a page. Something was hanging up or loading slowly.
Today, with 10.9.2, scrolling down the page finally feels “friction-free.” No beach balls or delays.
graphic drivers nothing?
Some may appreciate the more technical security notes from here:
http://support.apple.com/kb/HT6150
APPLE-SA-2014-02-25-1 OS X Mavericks 10.9.2 and Security Update
2014-001
OS X Mavericks 10.9.2 and Security Update 2014-001 is now available
and addresses the following:
Apache
Available for: OS X Lion v10.7.5, OS X Lion Server v10.7.5,
OS X Mountain Lion v10.8.5, OS X Mavericks 10.9 and 10.9.1
Impact: Multiple vulnerabilities in Apache
Description: Multiple vulnerabilities existed in Apache, the most
serious of which may lead to cross-site scripting. These issues were
addressed by updating Apache to version 2.2.26.
CVE-ID
CVE-2013-1862
CVE-2013-1896
App Sandbox
Available for: OS X Mountain Lion v10.8.5
Impact: The App Sandbox may be bypassed
Description: The LaunchServices interface for launching an
application allowed sandboxed apps to specify the list of arguments
passed to the new process. A compromised sandboxed application could
abuse this to bypass the sandbox. This issue was addressed by
preventing sandboxed applications from specifying arguments. This
issue does not affect systems running OS X Mavericks 10.9 or later.
CVE-ID
CVE-2013-5179 : Friedrich Graeter of The Soulmen GbR
ATS
Available for: OS X Mountain Lion v10.8.5,
OS X Mavericks 10.9 and 10.9.1
Impact: Viewing or downloading a document containing a maliciously
crafted embedded font may lead to arbitrary code execution
Description: A memory corruption issue existed in the handling of
handling of Type 1 fonts. This issue was addressed through improved
bounds checking.
CVE-ID
CVE-2014-1254 : Felix Groebert of the Google Security Team
ATS
Available for: OS X Mavericks 10.9 and 10.9.1
Impact: The App Sandbox may be bypassed
Description: A memory corruption issue existed in the handling of
Mach messages passed to ATS. This issue was addressed through
improved bounds checking.
CVE-ID
CVE-2014-1262 : Meder Kydyraliev of the Google Security Team
ATS
Available for: OS X Mavericks 10.9 and 10.9.1
Impact: The App Sandbox may be bypassed
Description: An arbitrary free issue existed in the handling of Mach
messages passed to ATS. This issue was addressed through additional
validation of Mach messages.
CVE-ID
CVE-2014-1255 : Meder Kydyraliev of the Google Security Team
ATS
Available for: OS X Lion v10.7.5, OS X Lion Server v10.7.5,
OS X Mountain Lion v10.8.5, OS X Mavericks 10.9 and 10.9.1
Impact: The App Sandbox may be bypassed
Description: A buffer overflow issue existed in the handling of Mach
messages passed to ATS. This issue was addressed by additional bounds
checking.
CVE-ID
CVE-2014-1256 : Meder Kydyraliev of the Google Security Team
Certificate Trust Policy
Available for: OS X Lion v10.7.5, OS X Lion Server v10.7.5,
OS X Mountain Lion v10.8.5, OS X Mavericks 10.9 and 10.9.1
Impact: Root certificates have been updated
Description: The set of system root certificates has been updated.
The complete list of recognized system roots may be viewed via the
Keychain Access application.
CFNetwork Cookies
Available for: OS X Mountain Lion v10.8.5
Impact: Session cookies may persist even after resetting Safari
Description: Resetting Safari did not always delete session cookies
until Safari was closed. This issue was addressed through improved
handling of session cookies. This issue does not affect systems
running OS X Mavericks 10.9 or later.
CVE-ID
CVE-2014-1257 : Rob Ansaldo of Amherst College, Graham Bennett
CoreAnimation
Available for: OS X Mountain Lion v10.8.5,
OS X Mavericks 10.9 and 10.9.1
Impact: Visiting a maliciously crafted site may lead to an
unexpected application termination or arbitrary code execution
Description: A heap buffer overflow existed in CoreAnimation’s
handling of images. This issue was addressed through improved bounds
checking.
CVE-ID
CVE-2014-1258 : Karl Smith of NCC Group
CoreText
Available for: OS X Mavericks 10.9 and 10.9.1
Impact: Applications that use CoreText may be vulnerable to an
unexpected application termination or arbitrary code execution
Description: A signedness issue existed in CoreText in the handling
of Unicode fonts. This issue is addressed through improved bounds
checking.
CVE-ID
CVE-2014-1261 : Lucas Apa and Carlos Mario Penagos of IOActive Labs
curl
Available for: OS X Mavericks 10.9 and 10.9.1
Impact: An attacker with a privileged network position may intercept
user credentials or other sensitive information
Description: When using curl to connect to an HTTPS URL containing
an IP address, the IP address was not validated against the
certificate. This issue does not affect systems prior to OS X
Mavericks v10.9.
CVE-ID
CVE-2014-1263 : Roland Moriz of Moriz GmbH
Data Security
Available for: OS X Mavericks 10.9 and 10.9.1
Impact: An attacker with a privileged network position may capture
or modify data in sessions protected by SSL/TLS
Description: Secure Transport failed to validate the authenticity of
the connection. This issue was addressed by restoring missing
validation steps.
CVE-ID
CVE-2014-1266
Date and Time
Available for: OS X Lion v10.7.5, OS X Lion Server v10.7.5,
OS X Mountain Lion v10.8.5, OS X Mavericks 10.9 and 10.9.1
Impact: An unprivileged user may change the system clock
Description: This update changes the behavior of the systemsetup
command to require administrator privileges to change the system
clock.
CVE-ID
CVE-2014-1265
File Bookmark
Available for: OS X Lion v10.7.5, OS X Lion Server v10.7.5,
OS X Mountain Lion v10.8.5, OS X Mavericks 10.9 and 10.9.1
Impact: Viewing a file with a maliciously crafted name may lead to
an unexpected application termination or arbitrary code execution
Description: A buffer overflow existed in the handling of file
names. This issue was addressed through improved bounds checking.
CVE-ID
CVE-2014-1259
Finder
Available for: OS X Mavericks 10.9 and 10.9.1
Impact: Accessing a file’s ACL via Finder may lead to other users
gaining unauthorized access to files
Description: Accessing a file’s ACL via Finder may corrupt the ACLs
on the file. This issue was addressed through improved handling of
ACLs.
CVE-ID
CVE-2014-1264
ImageIO
Available for: OS X Lion v10.7.5, OS X Lion Server v10.7.5,
OS X Mountain Lion v10.8.5, OS X Mavericks 10.9 and 10.9.1
Impact: Viewing a maliciously crafted JPEG file may lead to the
disclosure of memory contents
Description: An uninitialized memory access issue existed in
libjpeg’s handling of JPEG markers, resulting in the disclosure of
memory contents. This issue was addressed by better JPEG handling.
CVE-ID
CVE-2013-6629 : Michal Zalewski
IOSerialFamily
Available for: OS X Lion v10.7.5, OS X Lion Server v10.7.5,
OS X Mountain Lion v10.8.5
Impact: Executing a malicious application may result in arbitrary
code execution within the kernel
Description: An out of bounds array access existed in the
IOSerialFamily driver. This issue was addressed through additional
bounds checking. This issue does not affect systems running OS X
Mavericks v10.9 or later.
CVE-ID
CVE-2013-5139 : @dent1zt
LaunchServices
Available for: OS X Lion v10.7.5, OS X Lion Server v10.7.5,
OS X Mountain Lion v10.8.5
Impact: A file could show the wrong extension
Description: An issue existed in the handling of certain unicode
characters that could allow filenames to show incorrect extensions.
The issue was addressed by filtering unsafe unicode characters from
display in filenames. This issue does not affect systems running OS X
Mavericks v10.9 or later.
CVE-ID
CVE-2013-5178 : Jesse Ruderman of Mozilla Corporation, Stephane Sudre
of Intego
NVIDIA Drivers
Available for: OS X Lion v10.7.5, OS X Lion Server v10.7.5,
OS X Mountain Lion v10.8.5, OS X Mavericks 10.9 and 10.9.1
Impact: Executing a malicious application could result in arbitrary
code execution within the graphics card
Description: An issue existed that allowed writes to some trusted
memory on the graphics card. This issue was addressed by removing the
ability of the host to write to that memory.
CVE-ID
CVE-2013-5986 : Marcin Kościelnicki from the X.Org Foundation
Nouveau project
CVE-2013-5987 : Marcin Kościelnicki from the X.Org Foundation
Nouveau project
PHP
Available for: OS X Lion v10.7.5, OS X Lion Server v10.7.5,
OS X Mountain Lion v10.8.5, OS X Mavericks 10.9 and 10.9.1
Impact: Multiple vulnerabilities in PHP
Description: Multiple vulnerabilities existed in PHP, the most
serious of which may have led to arbitrary code execution. These
issues were addressed by updating PHP to version 5.4.22 on OS X
Mavericks v10.9, and 5.3.28 on OS X Lion and Mountain Lion.
CVE-ID
CVE-2013-4073
CVE-2013-4113
CVE-2013-4248
CVE-2013-6420
QuickLook
Available for: OS X Mountain Lion v10.8.5
Impact: Downloading a maliciously crafted Microsoft Office file may
lead to an unexpected application termination or arbitrary code
execution
Description: A memory corruption issue existed in QuickLook’s
handling of Microsoft Office files. Downloading a maliciously crafted
Microsoft Office file may have led to an unexpected application
termination or arbitrary code execution. This issue does not affect
systems running OS X Mavericks 10.9 or later.
CVE-ID
CVE-2014-1260 : Felix Groebert of the Google Security Team
QuickLook
Available for: OS X Mountain Lion v10.8.5,
OS X Mavericks 10.9 and 10.9.1
Impact: Downloading a maliciously crafted Microsoft Word document
may lead to an unexpected application termination or arbitrary code
execution
Description: A double free issue existed in QuickLook’s handling of
Microsoft Word documents. This issue was addressed through improved
memory management.
CVE-ID
CVE-2014-1252 : Felix Groebert of the Google Security Team
QuickTime
Available for: OS X Lion v10.7.5, OS X Lion Server v10.7.5,
OS X Mountain Lion v10.8.5, OS X Mavericks 10.9 and 10.9.1
Impact: Playing a maliciously crafted movie file may lead to an
unexpected application termination or arbitrary code execution
Description: A buffer overflow existed in the handling of ‘ftab’
atoms. This issue was addressed through improved bounds checking.
CVE-ID
CVE-2014-1246 : An anonymous researcher working with HP’s Zero Day
Initiative
QuickTime
Available for: OS X Lion v10.7.5, OS X Lion Server v10.7.5,
OS X Mountain Lion v10.8.5, OS X Mavericks 10.9 and 10.9.1
Impact: Playing a maliciously crafted movie file may lead to an
unexpected application termination or arbitrary code execution
Description: A memory corruption issue existed in the handling of
‘dref’ atoms. This issue was addressed through improved bounds
checking.
CVE-ID
CVE-2014-1247 : Tom Gallagher & Paul Bates working with HP’s Zero Day
Initiative
QuickTime
Available for: OS X Lion v10.7.5, OS X Lion Server v10.7.5,
OS X Mountain Lion v10.8.5, OS X Mavericks 10.9 and 10.9.1
Impact: Playing a maliciously crafted movie file may lead to an
unexpected application termination or arbitrary code execution
Description: A buffer overflow existed in the handling of ‘ldat’
atoms. This issue was addressed through improved bounds checking.
CVE-ID
CVE-2014-1248 : Jason Kratzer working with iDefense VCP
QuickTime
Available for: OS X Lion v10.7.5, OS X Lion Server v10.7.5,
OS X Mountain Lion v10.8.5, OS X Mavericks 10.9 and 10.9.1
Impact: Viewing a maliciously crafted PSD image may lead to an
unexpected application termination or arbitrary code execution
Description: A buffer overflow existed in the handling of PSD
images. This issue was addressed through improved bounds checking.
CVE-ID
CVE-2014-1249 : dragonltx of Tencent Security Team
QuickTime
Available for: OS X Lion v10.7.5, OS X Lion Server v10.7.5,
OS X Mountain Lion v10.8.5, OS X Mavericks 10.9 and 10.9.1
Impact: Playing a maliciously crafted movie file may lead to an
unexpected application termination or arbitrary code execution
Description: An out of bounds byte swapping issue existed in the
handling of ‘ttfo’ elements. This issue was addressed through
improved bounds checking.
CVE-ID
CVE-2014-1250 : Jason Kratzer working with iDefense VCP
QuickTime
Available for: OS X Lion v10.7.5, OS X Lion Server v10.7.5,
OS X Mountain Lion v10.8.5, OS X Mavericks 10.9 and 10.9.1
Impact: Playing a maliciously crafted movie file may lead to an
unexpected application termination or arbitrary code execution
Description: A signedness issue existed in the handling of ‘stsz’
atoms. This issue was addressed through improved bounds checking.
CVE-ID
CVE-2014-1245 : Tom Gallagher & Paul Bates working with HP’s Zero Day
Initiative
Secure Transport
Available for: OS X Mountain Lion v10.8.5
Impact: An attacker may be able to decrypt data protected by SSL
Description: There were known attacks on the confidentiality of SSL
3.0 and TLS 1.0 when a cipher suite used a block cipher in CBC mode.
To address these issues for applications using Secure Transport, the
1-byte fragment mitigation was enabled by default for this
configuration.
CVE-ID
CVE-2011-3389 : Juliano Rizzo and Thai Duong
OS X Mavericks v10.9.2 includes the content of Safari 7.0.2.
OS X Mavericks v10.9.2 and Security Update 2014-001 may be obtained from
the Mac App Store or Apple’s Software Downloads web site:
http://www.apple.com/support/downloads/
Uh, I don’t mean to be a nitpick, but there’s really no need to repost the ENTIRE CONTENT OF THE PAGE YOU PROVIDED THE LINK FOR.
Apple also released security patches for Lion and Mountain Lion. Does this mean the SSL bug is present in those versions as well?
That is correct. Though the issue focused on OS X Mavericks, OS X Lion and OS X Mountain Lion have separate patches because they are also vulnerable.
Please god let the Gmail-IMAP / Mail clusterflock be fixed. Not that I give a poo, personally, since I don’t use Gmail — but most of my clients do, at least until I talk them into acquiring a domain and saying Adios Motherflocker to Google.
For the record: I did not say ‘clusterflock’ nor did I say ‘poo’, but I did use a strategic asterisk in a few places in the vain hope of placating the apparently-Victorian-era-censors over there. Forchrisake, we’re not on the Mike Huckabee show here. Or maybe we are.
Hey Grey, I had to edit some of your colorful word choices to pass through our comment filters. In some situations, asterisks placed correctly work to get through, but usually it’s fairly restrictive. In general, we try to aim for a PG commenting thread since there are a very wide variety of readers here, but many of the filtering restrictions are aimed at anti-spam measures too.
Anyway, thanks for reading and commenting, and let us know how updating to OS X 10.9.2 works out for you :)
F*ck it.
Smileyface.
I’m still having the same old problem with Mail not getting new gmail. My main acct is @mac.com but I use gmail a lot too. This problem didn’t occur until Mavericks cam along. No problem with mac.com but with gmail the Get Mail button doesn’t get new mail, so have to completely close out of Mail and re-open. BTW, using os 19.9.2.
Is anyone else still having this problem?
Sorry, my OS is actually 10.9.2.
beat me to it DG. NERD!!! *wedgie and noogie
…….Adds additional layers of awesomeness to OSXDaily.com readers who read release notes
LOL!
:)
We gotta put a little something in there for the thorough readers, right?
I was reading and then “WHAT?”, hahaha!
Hahahaa love it!