How to Log Off Another Users ssh Connection by Command Line in Mac OS or Linux

Using SSH, or Secure Shell, is a very common way to establish remote connections to Mac and Linux machines from the command line. If you’re a systems administrator, or if you have SSH enabled on a Mac for another reason, you may eventually need to log off another users ssh connection. There are several ways to end a users ssh connection to a Mac (or Linux box for that matter, these tips apply equally there too), and we’ll cover a few of them.
Note these approaches will work to log off a users ssh connection, regardless of how you enabled SSH on the computer. Whether the Mac is enabling ssh with Remote Login or enabling ssh by command line does not matter for these purposes. Likewise, these tricks are written with MacOS and Mac OS X in mind but apply equally to terminating ssh user processes in Linux and most other Unix flavors as well.
How to Log Off a Users ssh Connection
Perhaps the most common way to log out a user connected via ssh is by using the kill or pkill commands, either targeting the specific ssh process in question, or the user account directly.
Logging Out ssh User with kill
First, get the process ID (PID) of the users ssh connection:
ps aux | grep sshd
Next, locate the specific process of the target users ssh connection and target that with kill -9. For example let’s assume we want to terminate the user Walrus’s ssh connection and the process for ‘sshd: Walrus@ttys011’ has a PID of 5821:
kill -9 5821
The effect is instant and the on the users end they will see a message at their terminal screen stating: “Connection to localhost closed by remote host.Connection to localhost closed.”
Broadly Ending a Users SSH Connection and Related Processes with pkill
Another broader approach is to kill all processes belonging to a specific user account with pkill, this allows you to simply target a user account rather than a process ID:
pkill -u username
This will instantly log out the user ‘username’ by terminating all of that users processes.
The pkill approach is useful because it also accepts wildcards and you can also easily target a process by name if you want to broadly terminate all ssh processes for example.
There are other possibilities for terminating another users ssh connection, but the above tricks are perhaps the most intuitive for savvy command line users. Basically any method that allows you to see the running processes and locate the expected users ssh connection will work to achieve the same effect; ending that process will result in logging off that user from ssh.
Logging Off SSH User from a Mac with Activity Monitor
If you’re a Mac user who prefers to stay in the GUI, then you can also use Activity Monitor to locate the task of and terminate it that way, the same way you would be force quitting Mac apps in general. Simply open Activity Monitor, search for ‘ssh’ and find the users ssh connection you wish to end, then terminate that process through Activity Monitor.
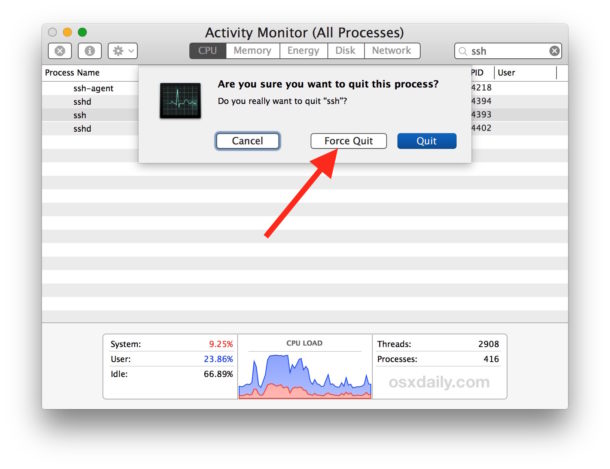
Since this approach uses Activity Monitor, a native Mac utility, this method obviously won’t work for linux machines as they don’t have that utility, whereas any other approach to target the process would.
And just in case you’re wondering, yes all of this would work basically the same with telnet, Screen Sharing, or any other remote connection method, by targeting those relevant processes specific to the logged in user account.
If you know of any other methods or approaches to logging out user ssh connections or disconnecting users from ssh, share with us in the comments below!


Typically you would want to kill all processes the user has launched from that ssh session, so what I do is use “w” to get the device they’re logged in on and then:
fuser -k /dev/
Old UNIX Guy
Kill -1 or sending hup to their bash process is much better than kill. It should logout from an idle bash session, and write history on the way out – not something that happens when you kill.
Why kill -9 ? Never kill -9, that should be a measure of last resort.
I suppose to guarantee that the SSH session has ended, if the kill is to be successful -9 will certainly do it. I think many sysadmins just default to using -9 when no flag or -3 or -6 would do the trick. What would be your preference? Soft kill?
I personally would use the pkill approach for achieving the desired effect, because I wouldn’t care if it was applied broadly if the intention is to log out the user, might as well end all their processes even anything screen’d. But there could be a better way, I haven’t been an admin for anything with outside access let alone something that anyone would telnet or ssh into in a few years now :) Just manage my own hardware now.